Understanding Anonymous Email and Its Importance
What Is an Anonymous Email Account?
An anonymous email account is a service that allows you to send and receive emails without linking your identity to your personal data. These accounts are designed with privacy in mind, ensuring that no personal information—such as your name, phone number, or location—is required during registration. By keeping your email identity untraceable, you can communicate without worrying about tracking or data breaches.
The Need for Online Privacy
In an era of widespread surveillance and data mining, every online interaction can be recorded, analyzed, and potentially exploited. Anonymous email services provide a crucial layer of protection by:
-
Shielding your personal details from hackers and data brokers.
-
Preventing intrusive advertisements and targeted marketing.
-
Enabling whistleblowers, activists, or anyone needing discretion to communicate safely.
How Anonymous Email Differs from Traditional Email
Unlike conventional email providers, which often require personal information for account creation and might scan your emails for targeted ads, anonymous email services focus on privacy. They eliminate the need for personal data, offer end-to-end encryption, and generally have strict no-log policies, ensuring your digital communications remain private.
The Benefits of a Free Anonymous Email Setup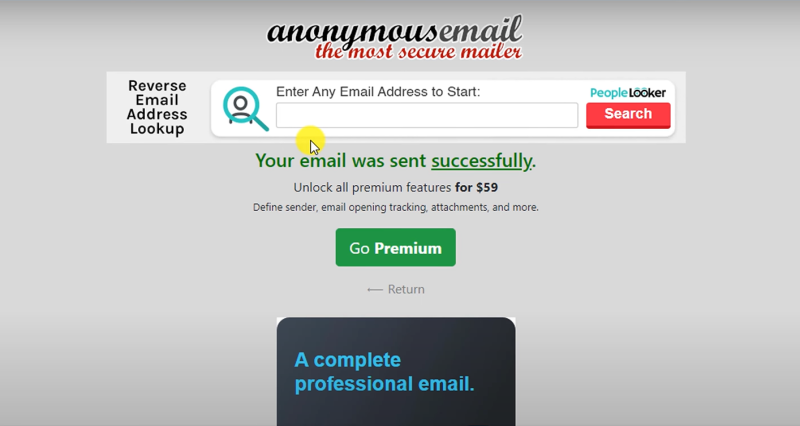
Privacy Without Cost
One of the most attractive aspects of free anonymous email accounts is that you don’t have to pay for enhanced privacy. Numerous providers offer robust, secure email services without the need for a subscription, making them accessible to anyone who values their privacy.
Enhanced Security Features
Even free anonymous email services come with a variety of security measures:
-
End-to-End Encryption: Ensures that only you and the intended recipient can read your messages.
-
No Personal Data Required: Registration is streamlined, avoiding the pitfalls of personal information exposure.
-
Ad-Free Environments: Many services avoid intrusive advertising, reducing the risk of tracking cookies and malware.
Flexible Use Cases
Whether you’re signing up for online forums, conducting sensitive business communications, or protecting your personal life from prying eyes, an anonymous email account offers the flexibility and security you need. It’s an essential tool for maintaining privacy in a world where your digital trail can be used against you.
Step-by-Step Guide to Creating Your Anonymous Email Account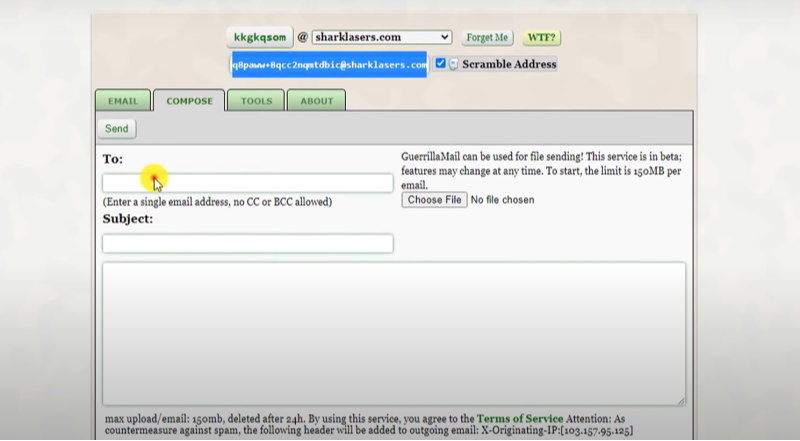
Choosing the Right Provider
Before you set up your anonymous email account, research providers that specialize in privacy. Look for services with strong encryption protocols, a clear no-logs policy, and positive user reviews. Compare features like:
-
Ease of registration without personal details.
-
Availability of secure protocols (e.g., SSL/TLS encryption).
-
Options for two-factor authentication (2FA) to further secure your account.
Registration Process: A Detailed Walkthrough
Step One: Visit the Provider’s Website
Navigate to the website of your chosen anonymous email provider. Look for a “Sign Up” or “Register” button, and click to begin the process.
Step Two: Complete the Registration Form
Since the goal is to remain anonymous, the registration form should not require personal details. Provide only the necessary information, such as your desired email username and a strong password. Some services might allow you to create a random username to further obscure your identity.
Step Three: Verify Your Account
Depending on the service, you might need to complete a verification process. This is typically done via a temporary email or CAPTCHA rather than linking to a phone number or secondary email address, which helps maintain your anonymity.
Step Four: Configure Security Settings
Once your account is active, navigate to the security settings. Enable two-factor authentication if available, set up recovery options that do not compromise your anonymity, and review any privacy policies to ensure they align with your needs.
Optimizing Your Anonymous Email Usage
Use a Unique Browser or Incognito Mode
For maximum privacy, consider accessing your anonymous email account using a dedicated browser or incognito/private browsing mode. This prevents cookies and browsing history from being linked back to your anonymous identity.
Avoid Using Personal Devices
If possible, use a device that isn’t tied to your personal identity. Public Wi-Fi networks or secure devices can help reduce the chances of your account being tracked through device fingerprints or IP addresses.
Regularly Update Your Security Settings
Stay proactive by reviewing your email account’s security settings periodically. Ensure that any software updates or security patches provided by the email service are promptly installed.
Advanced Security Measures for Email Anonymity
Utilizing Secure Email Tools
To further enhance your anonymity, consider integrating secure email tools:
-
PGP Encryption: Encrypt your emails using Pretty Good Privacy (PGP) to ensure that even if intercepted, your messages remain unreadable.
-
Anonymous Email Clients: Use email clients that prioritize privacy and do not store local data, ensuring your communications are as secure as possible.
Best Practices for Maintaining Anonymity
-
Don’t Reuse Usernames: Avoid using the same anonymous email across various services if linking accounts could compromise your identity.
-
Regularly Clear Browser Data: Clear cache and cookies to prevent websites from tracking your online activities.
-
Be Cautious with Attachments and Links: Even in an anonymous email, malicious attachments or links can compromise your device and reveal your identity.
💖Pro Tips💖
UFO VPN prioritizes your privacy by blocking ISPs, advertisers, and cybercriminals from harvesting data about your device or habits. Recognized as the best VPN for PC and best VPN for Mac, its advanced encryption anonymizes your connection, ensuring activities like visiting onion sites never reveal your hardware specs, browser fingerprints, or real IP address.
With one-click activation, UFO VPN simplifies security—no technical expertise needed. Start shielding your data by using best VPN for PC and browse with uncompromised confidence.
Integrating Best free VPN to Enhance Your Email Privacy
Why Use UFO VPN with Your Anonymous Email?
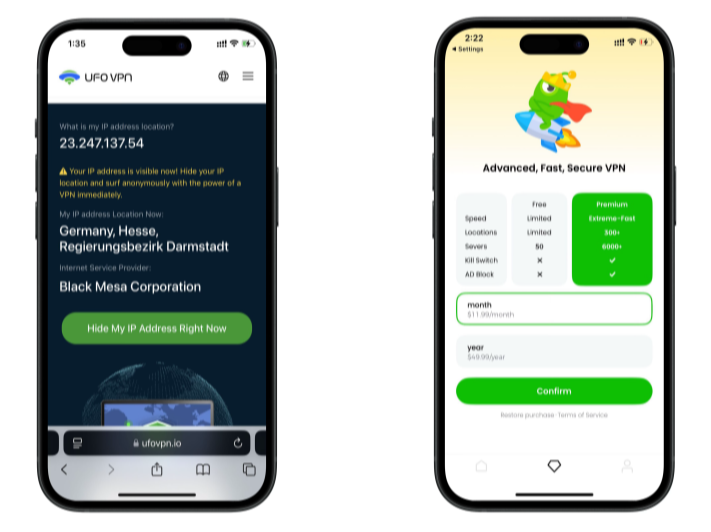
While a free anonymous email account provides significant privacy, coupling it with a robust VPN like UFO VPN adds an extra layer of security. UFO VPN encrypts your internet traffic and masks your IP address, ensuring that your online activities—whether checking email or browsing the web—remain completely private.
How UFO VPN Bolsters Your Privacy
-
Full Traffic Encryption: UFO VPN encrypts every bit of data leaving your device, meaning even if someone intercepts your connection, your email content remains secure.
-
IP Address Masking: By hiding your true IP address, UFO VPN makes it nearly impossible for trackers to link your anonymous email account to your physical location or identity.
-
Bypassing Geolocation Restrictions: Enjoy seamless access to your anonymous email account from anywhere in the world, free from regional restrictions or surveillance.
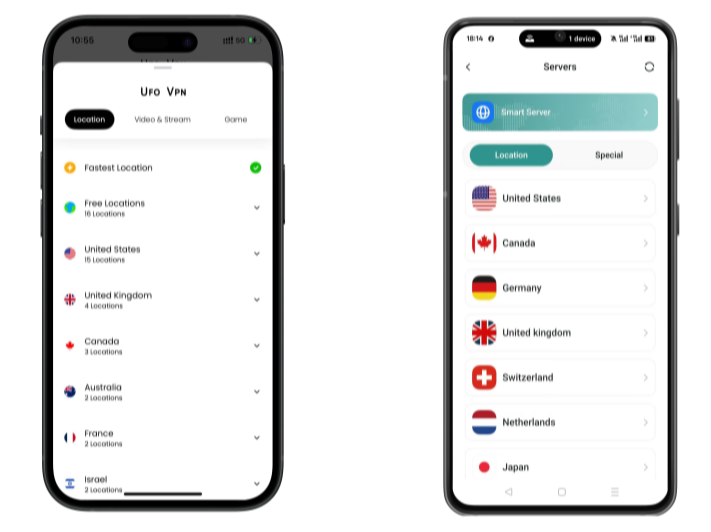
Steps to Set Up UFO VPN
With 3000+ server in over 100 countries, UFO VPN is open to download as a free iPhone VPN, free Android VPN(with VPN APK), free Windows VPN and free Mac VPN. Install the app and sign up or log in.
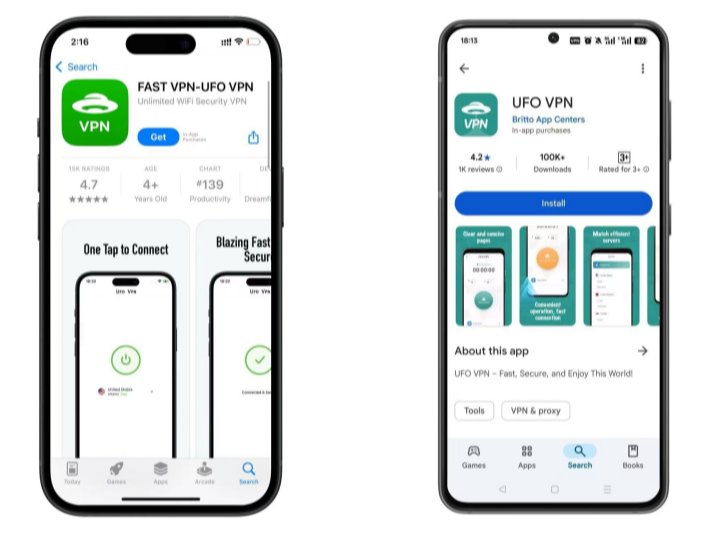
Open the app, choose a free server locationwhere your desired streaming/gaming/browsing platform is available.
We recommend free USA VPN, free UK VPN and free Australia VPN.
Pro Tip
UFO VPN is compatible with popular platforms in gaming and streaming as CODM VPN, PUBG VPN, Netflix VPN and more!
After connecting, visit What is My IP tool to see your current location and ensure your real IP is visible.
With all set, visit your favorite platform and start browsing without geo-blocks or buffering!
Frequently Asked Questions (FAQ)
How do I know if my anonymous email is truly untraceable?
The effectiveness of an anonymous email depends on both the provider’s security measures and your personal usage habits. Look for features such as no-log policies, end-to-end encryption, and minimal data requirements. Always use secure tools and a trusted VPN like UFO VPN to further mask your digital trail.
Is it safe to use a free anonymous email account for sensitive communications?
While free anonymous email services offer basic privacy, it’s crucial to pair them with additional security measures like strong encryption protocols and a reputable VPN. For highly sensitive communications, consider using advanced encryption tools in tandem with your anonymous account.
Do free anonymous email providers limit functionality compared to paid services?
Many free providers offer robust features that are sufficient for everyday use. However, paid services may provide additional features such as enhanced storage, priority support, or advanced security options. Your choice should depend on your specific privacy needs and usage patterns.
Can I use my anonymous email for signing up on multiple websites without being tracked?
Yes, that is one of the key benefits of using an anonymous email. Since no personal data is required during registration, you can use it across various platforms while keeping your identity concealed. Always remember to use privacy-enhancing tools like UFO VPN to ensure that your browsing and sign-up activities remain secure.
What additional steps can I take to safeguard my anonymous email account?
Beyond the initial setup, regular security audits, using incognito browsing modes, and pairing your email with a reliable VPN are critical steps. Regularly update your passwords and enable two-factor authentication where possible to ensure your account remains secure over time.
Conclusion
Building an untraceable email identity for free is not only possible—it’s essential in today’s digital landscape. By choosing a trusted free anonymous email provider and following best practices for secure communications, you can protect your personal information from prying eyes. Enhancing your email privacy with advanced tools like PGP encryption and anonymous email clients further fortifies your defenses.Moreover, integrating a robust VPN service such as UFO VPN adds an indispensable layer of security, encrypting your internet traffic and masking your IP address. This dual approach ensures that your communications remain private and your digital identity stays hidden from trackers, hackers, and surveillance agencies.
Embrace the power of anonymity and take control of your online privacy. With the right strategies and tools at your disposal, you can confidently navigate the digital world without compromising your personal security. Set up your free anonymous email account today, integrate it with UFO VPN, and enjoy a truly untraceable online identity.