What is a Zip Bomb?

A zip bomb, also known as a "decompression bomb", is a type of malicious archive file that is designed to overwhelm a system when opened. The zip bomb file itself may appear small (sometimes just a few kilobytes), but once decompressed, it expands into a massive amount of data. This creates a situation where the device’s storage or memory is overwhelmed, leading to potential crashes or slowdowns.
There are two main types of zip bombs:
-
Recursive Zip Bombs: These bombs consist of multiple nested zip files, each containing further zip files. When unpacked, they recursively unpack into massive files.
-
Non-Recursive Zip Bombs: These bombs are even more dangerous because they contain overlapping files that compress into extremely large sizes, such as 4.5 petabytes of data.
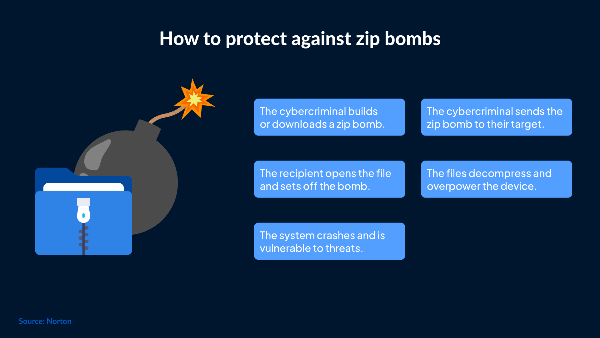
How Does a Zip Bomb Work?

A zip bomb exploits the compression algorithm used in file compression tools. By compressing files into zip archives, the file size can be drastically reduced. However, zip bombs take advantage of recursive compression to dramatically increase the decompressed size.
For example, a zip bomb might be only 42 KB in size but could expand to 4.5 petabytes once unzipped. This causes the target device to run out of space or crash due to the massive amount of data being extracted into memory.
The impact of a zip bomb depends on the size of the uncompressed data and the system's ability to handle such volume. A typical zip bomb is designed to:
-
Overload the Device: Cause the device to run out of storage or memory, leading to system crashes or slowdowns.
-
Disrupt Antivirus Software: By consuming resources, a zip bomb can prevent antivirus programs from detecting or responding to threats in real-time.
What Happens If You Open a Zip Bomb?
If you open or attempt to unpack a zip bomb, your device may experience severe performance degradation. The data overload can cause your system to freeze, slow down, or crash. For instance, opening a zip bomb that decompresses into petabytes of data could overwhelm the system’s storage or processing power, effectively making your device unusable until you resolve the issue.
Here’s how a zip bomb might affect your device:
-
Memory Overload: The system will try to allocate memory for the decompressed files, leading to errors and crashes.
-
Storage Exhaustion: The large size of the extracted files can fill up storage space, causing the device to become unresponsive.
-
Security Vulnerabilities: By exploiting system resources, zip bombs can create vulnerabilities that allow malware to enter the system unnoticed.
A Famous Example: The 42.zip File
One of the most infamous examples of a zip bomb is the 42.zip file. Despite being only 42 KB in size, this zip bomb contains recursive zip files that, when fully unpacked, would extract a whopping 4.5 petabytes of data. If you were to unpack this bomb, your system would run out of space, causing a crash or freeze.
This example illustrates how deceptively small zip bombs can be. Even though 42.zip is small in size, its decompressed state is so massive that it could bring down entire systems or delay the operation of antivirus software, allowing other malware or viruses to infiltrate.
Are Zip Bombs Dangerous?
Zip bombs can be extremely dangerous, especially if they manage to disrupt critical system processes or open up opportunities for malware. However, zip bombs are mostly harmful only when they are unpacked. The file itself poses no direct threat unless you attempt to unzip it.
Here’s why zip bombs can be dangerous:
-
Crashing Programs: They consume huge amounts of memory and processing power, making devices unusable.
-
Disrupting Security Software: The overload can slow or stop antivirus software, leaving your device vulnerable to other threats.
-
Data Loss: In extreme cases, zip bombs can cause data loss by overwhelming system resources and causing permanent errors.
While modern security software can detect and prevent zip bombs, it is important to remain vigilant and avoid interacting with suspicious files.
How to Protect Your Device from Zip Bombs
Here are some key steps you can take to protect your device from zip bombs and similar threats:
1. Avoid Downloading Suspicious Files
Never download files from untrusted or unknown sources. Zip bombs are often spread through phishing emails or malicious websites, so be cautious about opening attachments or clicking links in unsolicited messages.
2. Use Antivirus Software
Ensure your antivirus software is up to date and configured to detect malicious files like zip bombs. Most modern antivirus programs can detect and block zip bombs before they can do any damage.
3. Be Careful with File Compression
Be cautious when unzipping files from unknown or untrusted sources. You can use tools that scan the contents of a zip file before extracting it to ensure it doesn’t contain any malicious content.
4. Enable Security Features
Enable security features such as sandboxing or virtualization to isolate potentially harmful files. This allows you to analyze suspicious files without compromising your system.
5. Use a free proxy VPN in UFO VPN for Extra Protection
While zip bombs can attack local systems, UFO VPN offers another layer of protection by encrypting your internet traffic and preventing hackers from intercepting your data. Using a VPN will help protect your device from any online threats that could lead to downloading harmful files, such as zip bombs.
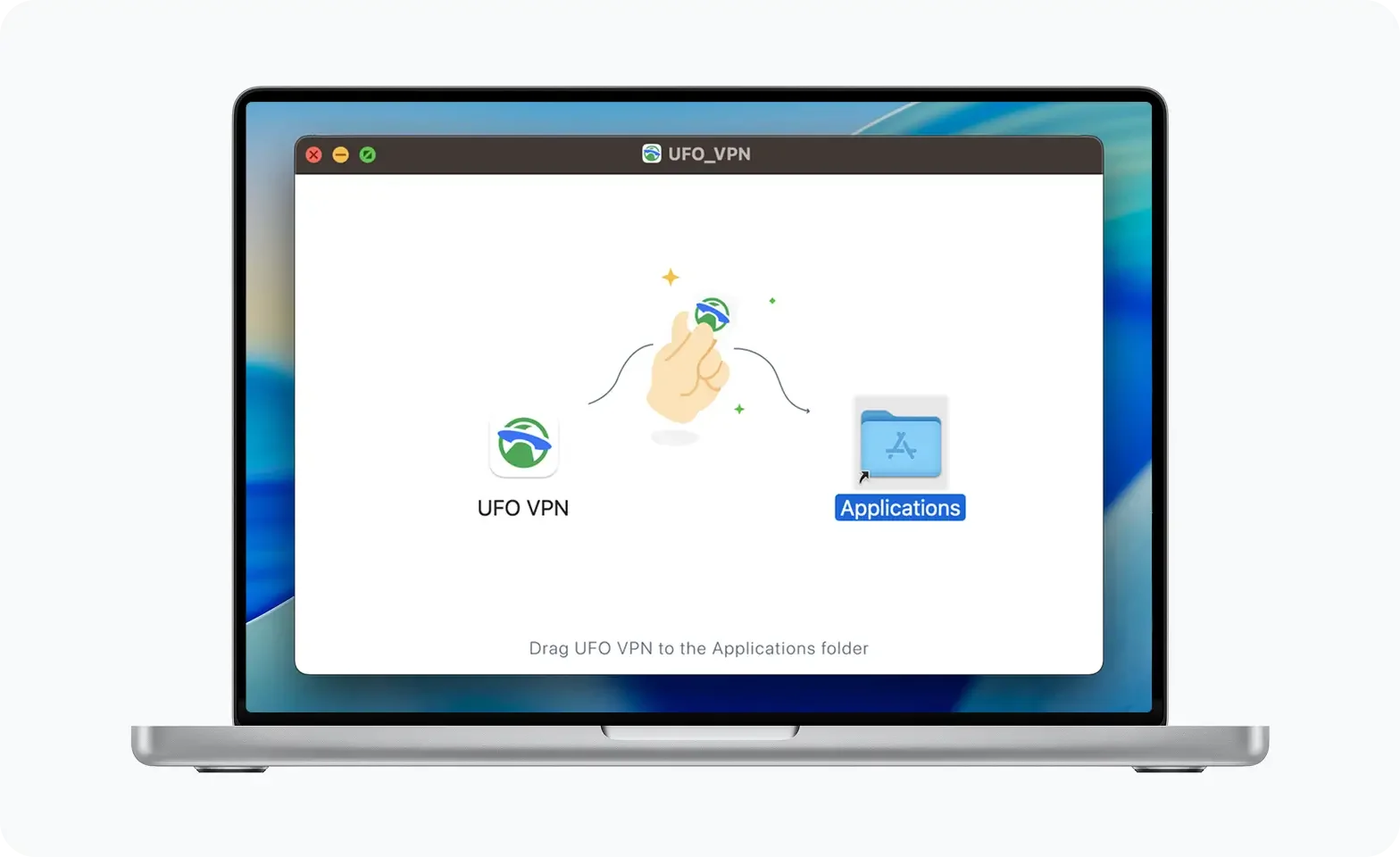
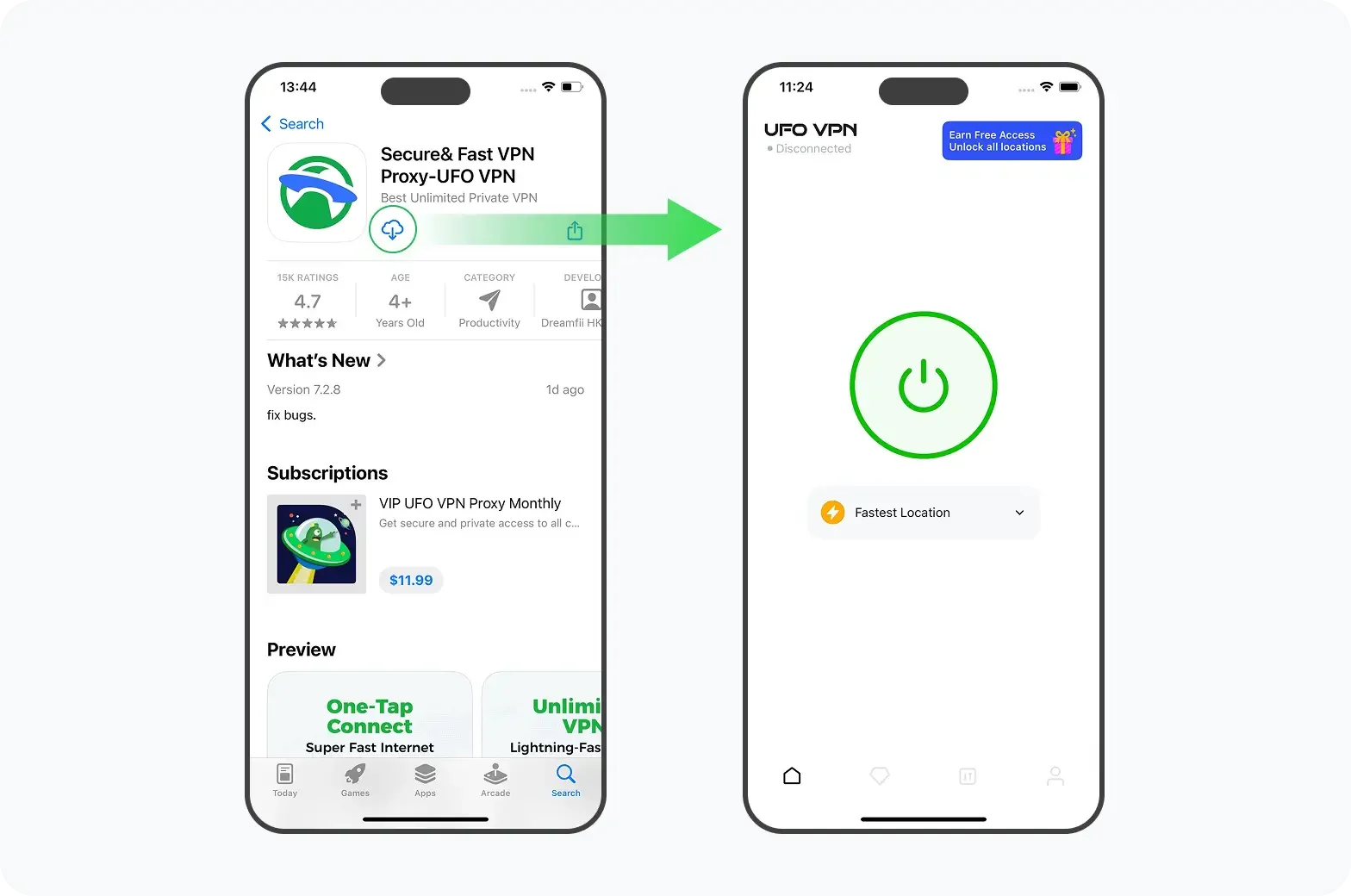
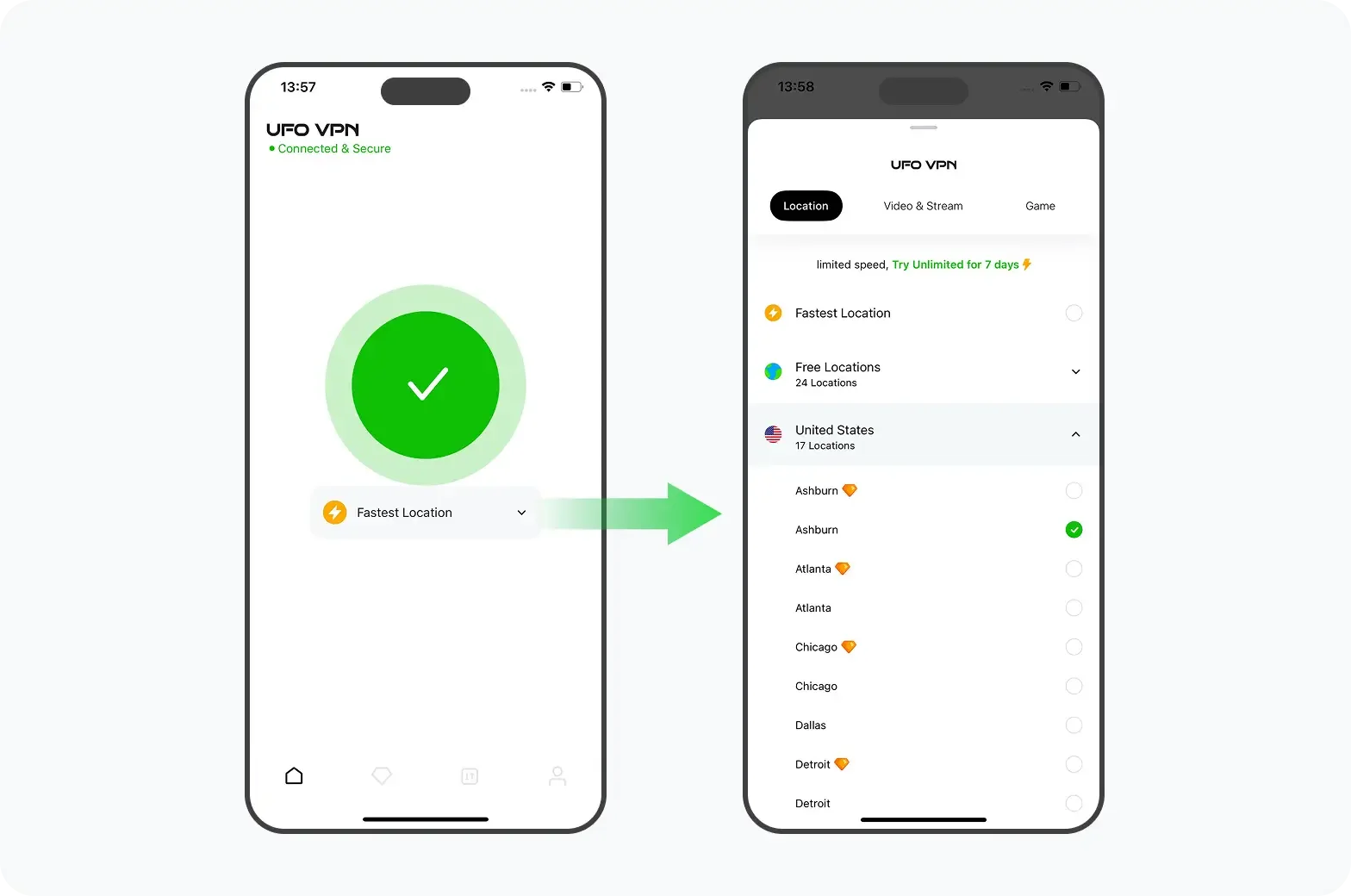
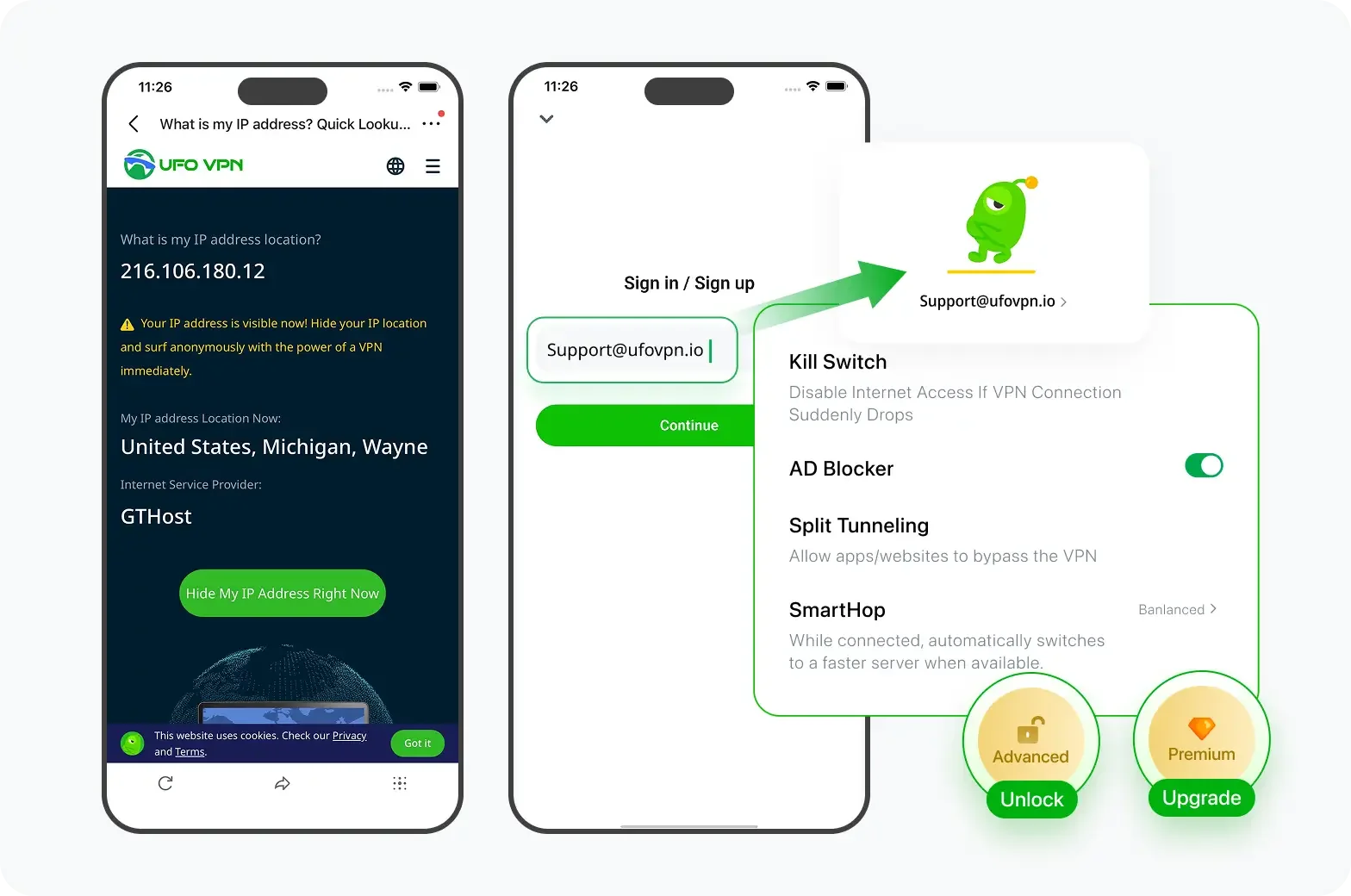
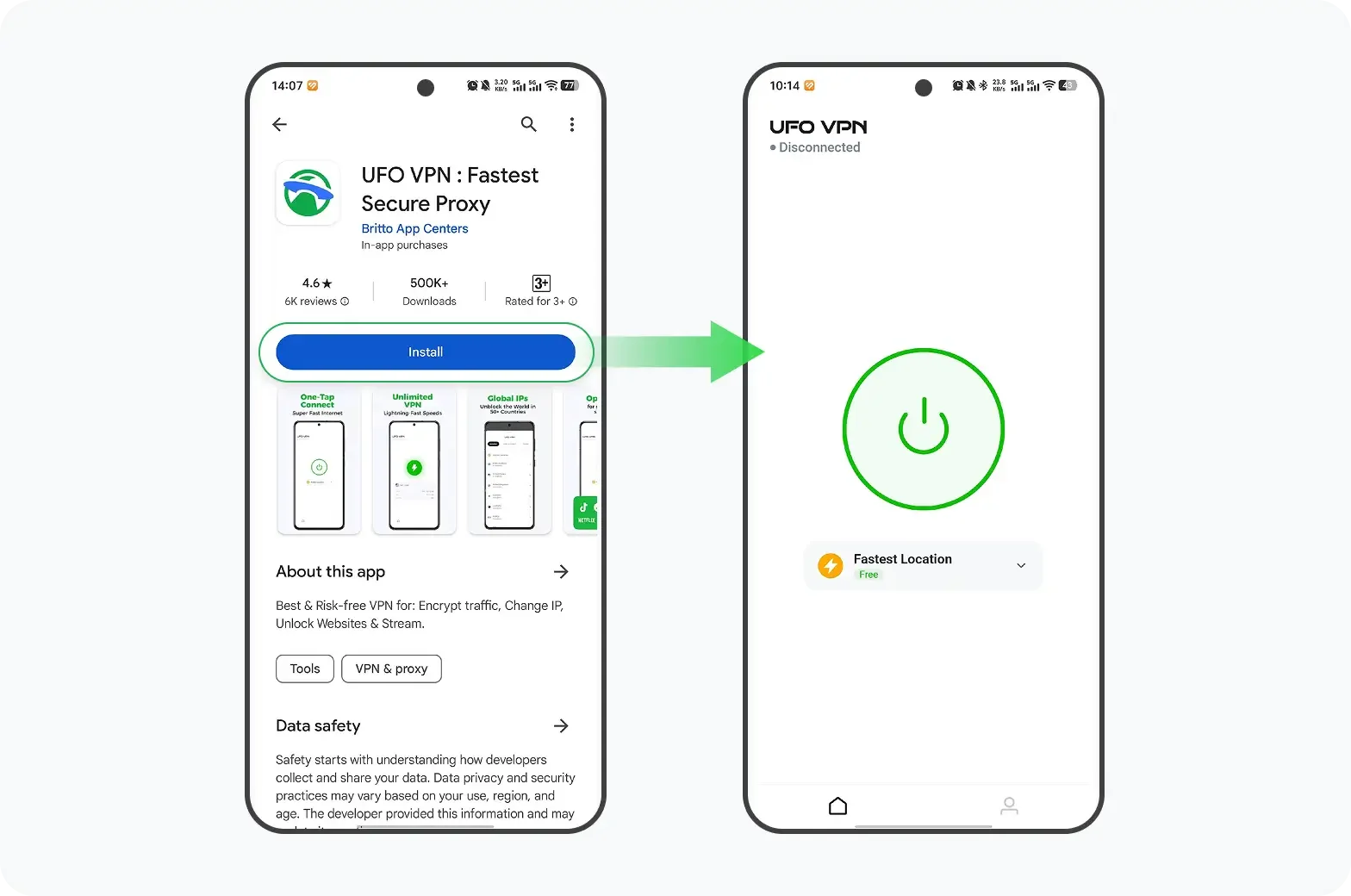
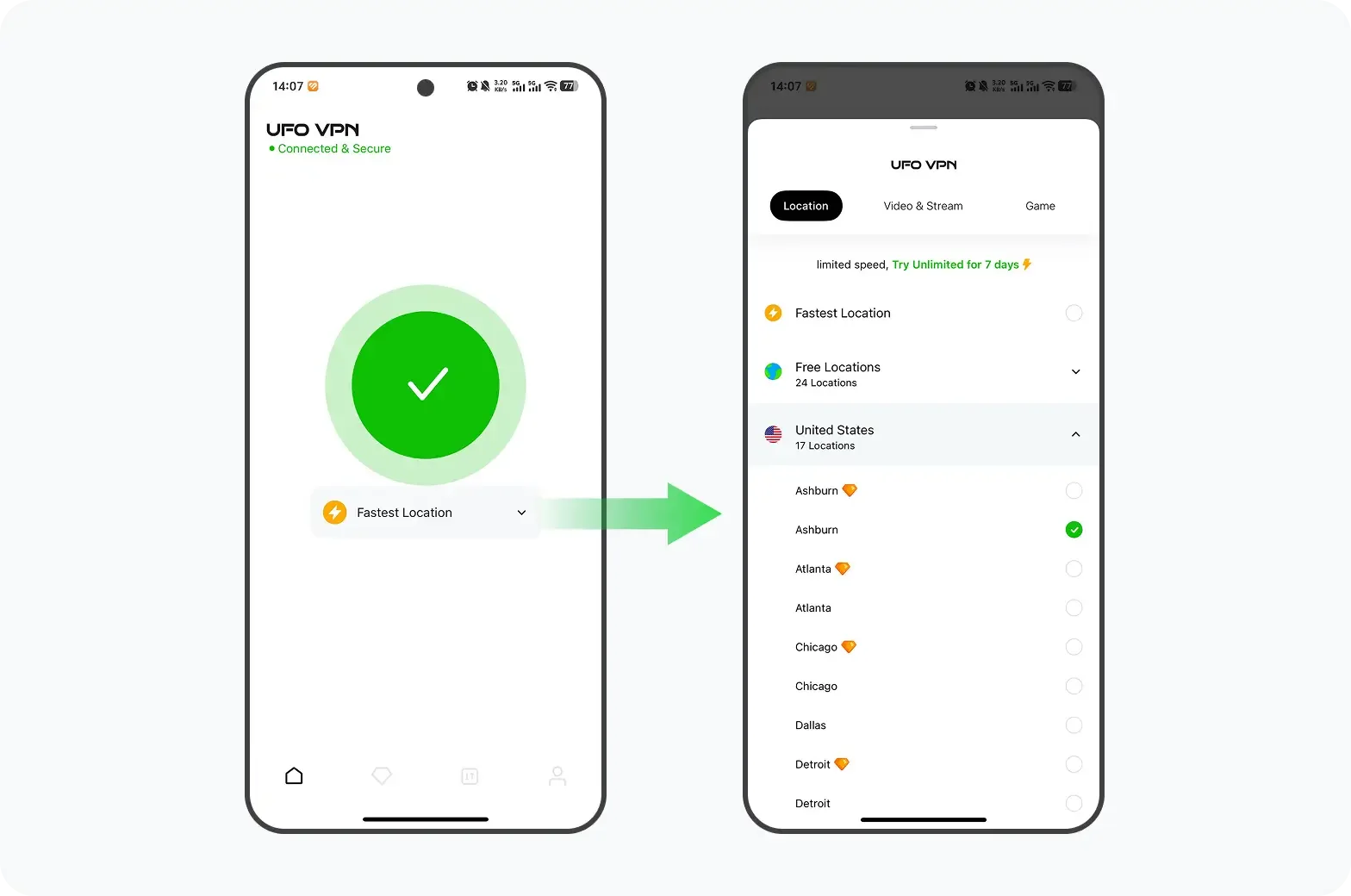
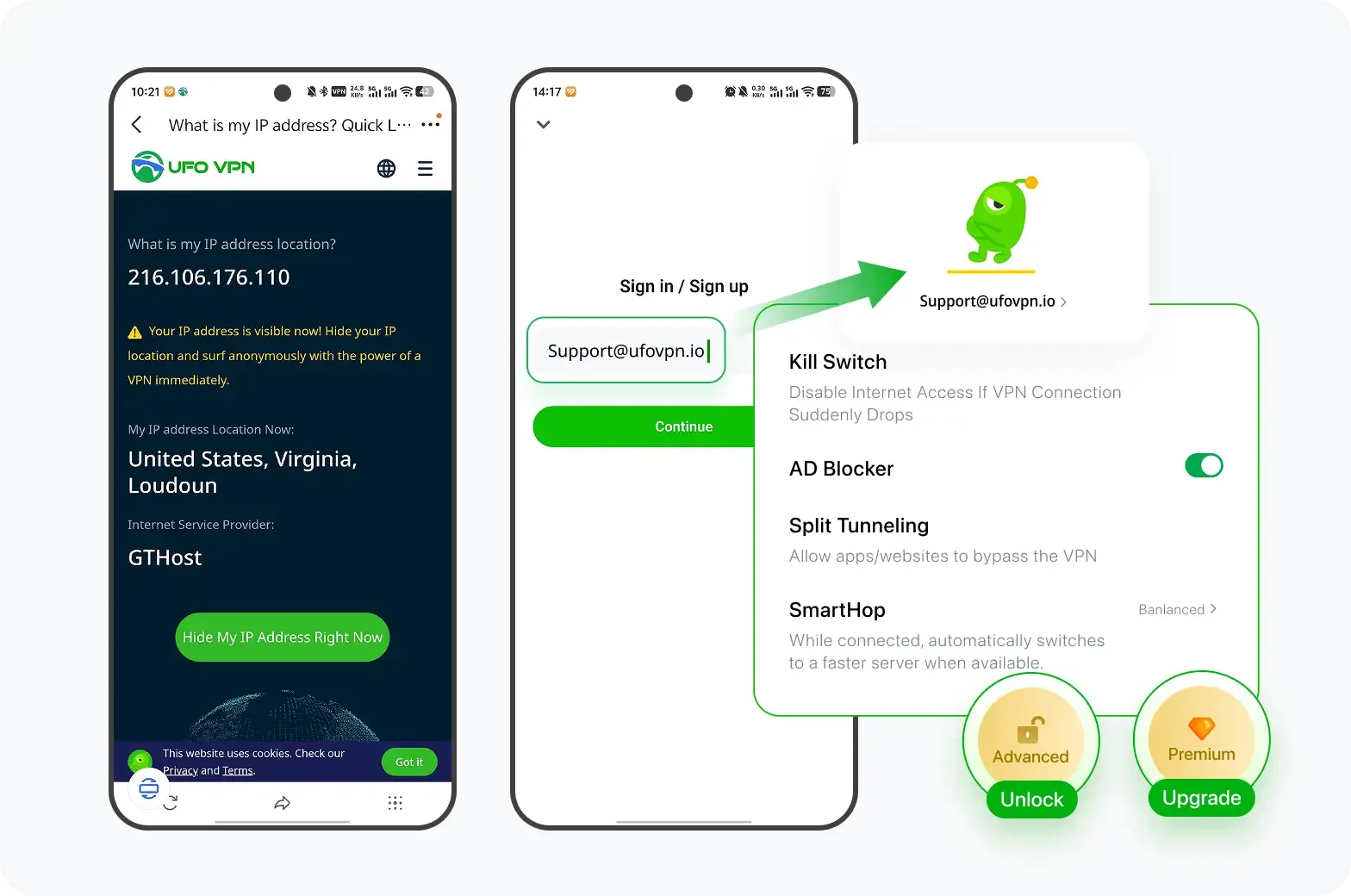
🩵Get Ready with UFO VPN in 4 Steps:
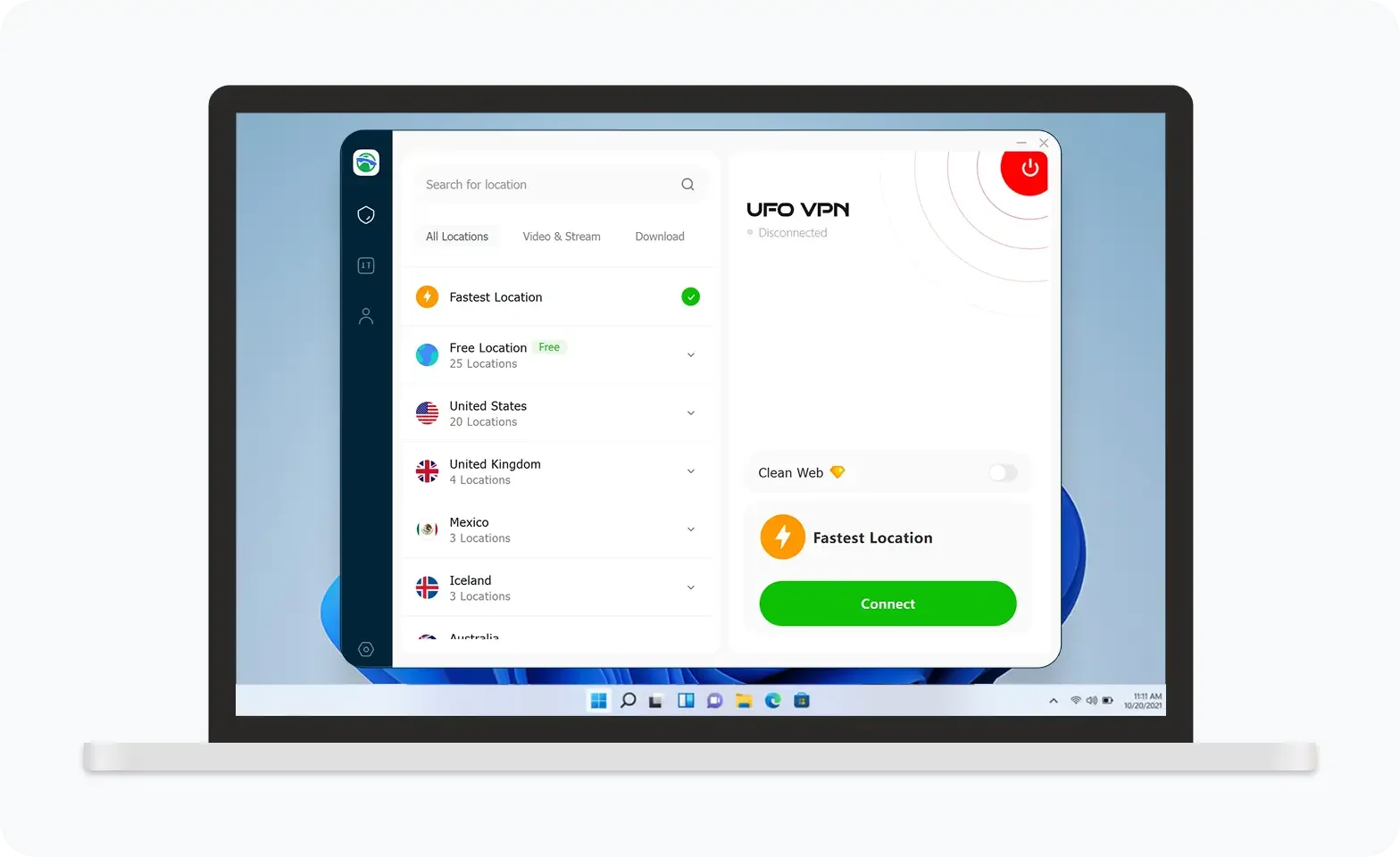
UFO VPN is an all-in-one VPN that offers unlimited access to 4K streaming like Netlfix, Disney Plus, no-ping gaming as PUBG, Roblox, CODM and social networking for YouTube, X, Facebook and more.
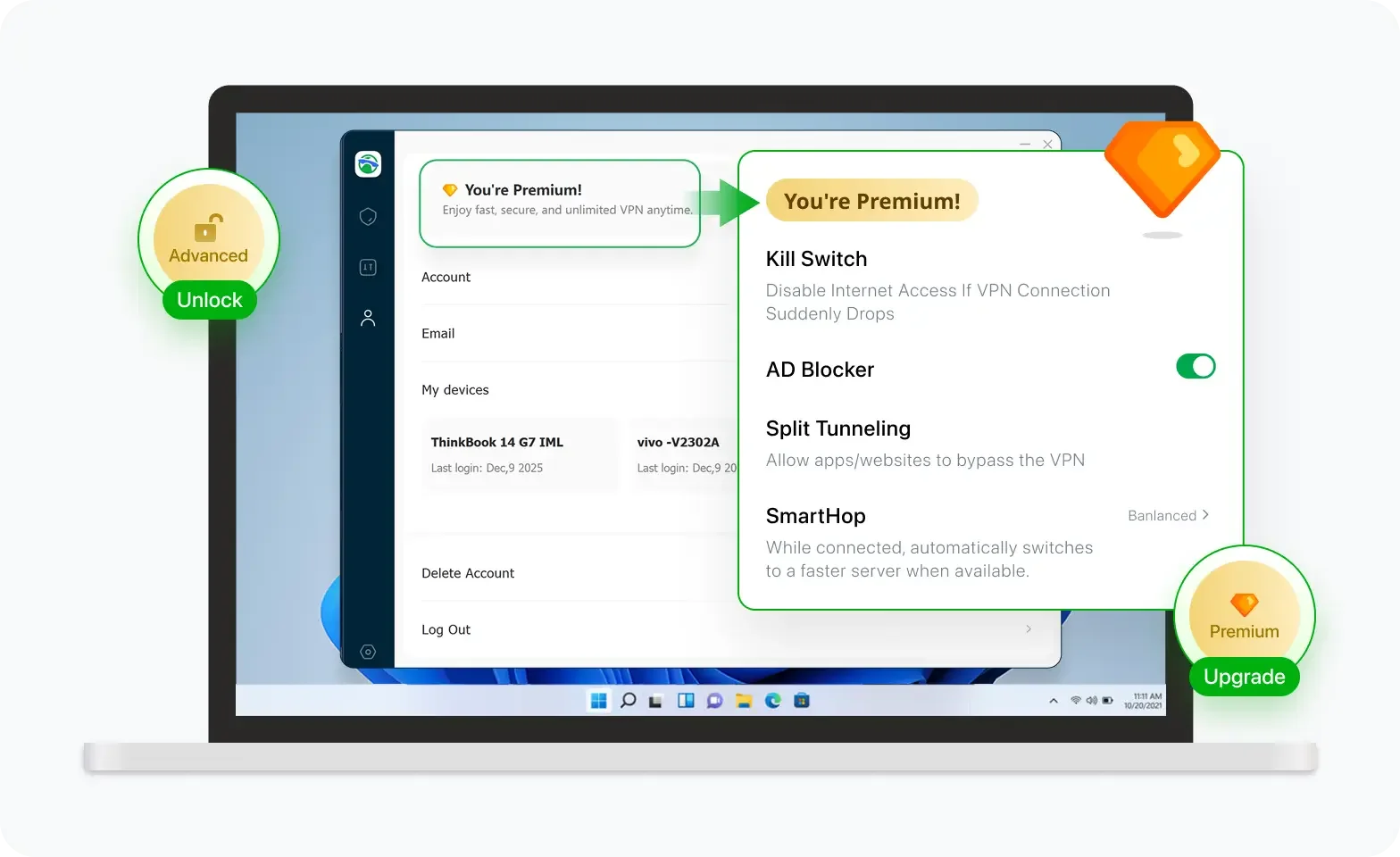
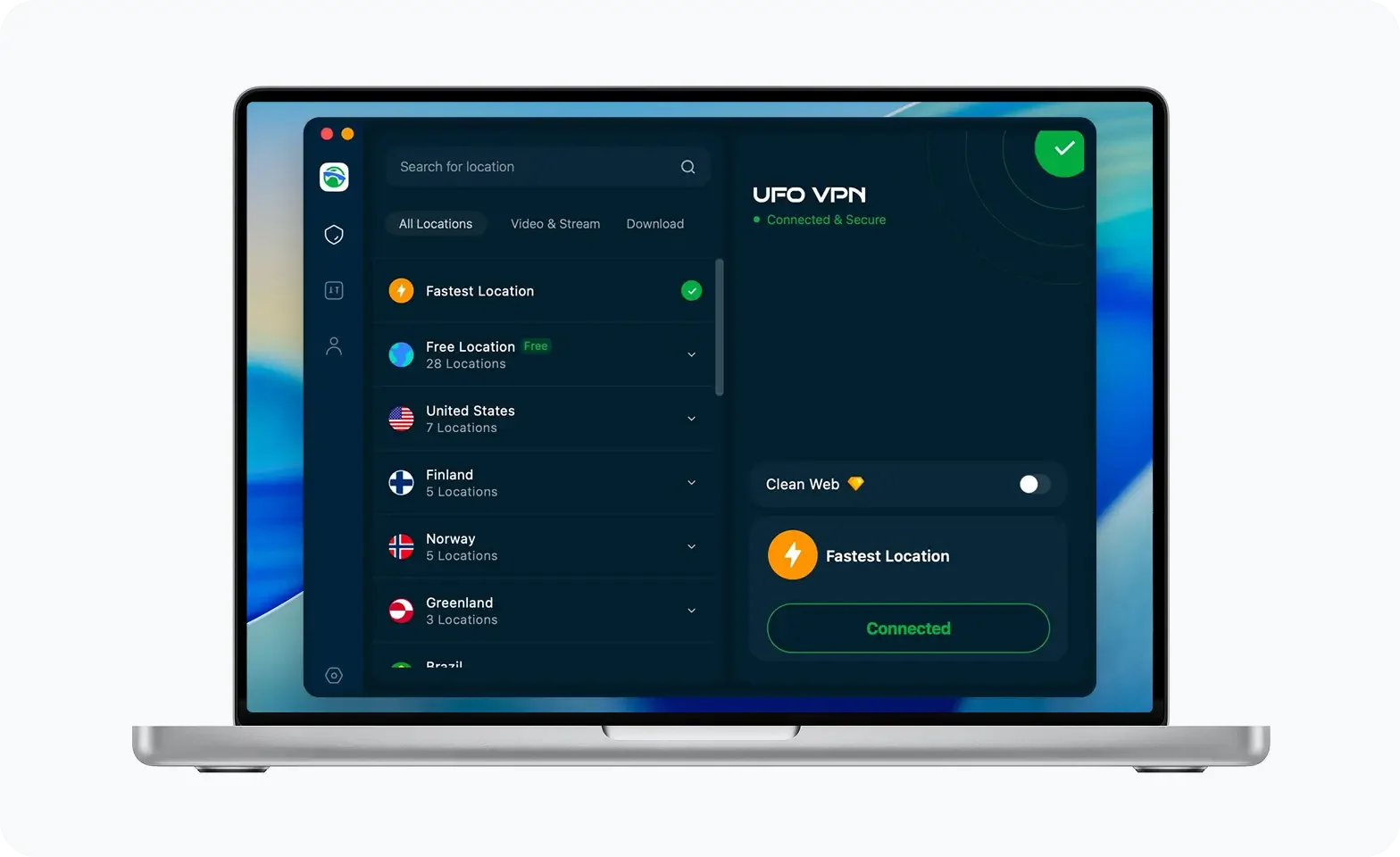
Unlock Pro Features
If you have upgraded to premium plan , feel free to enjoy premium servers for 4K streaming and advanced features like Kill Switch, Split Tunneling, and gaming acceleration. Your Mac is now fully optimized and protected. Inaddition to basic functions, we recommend you turn on

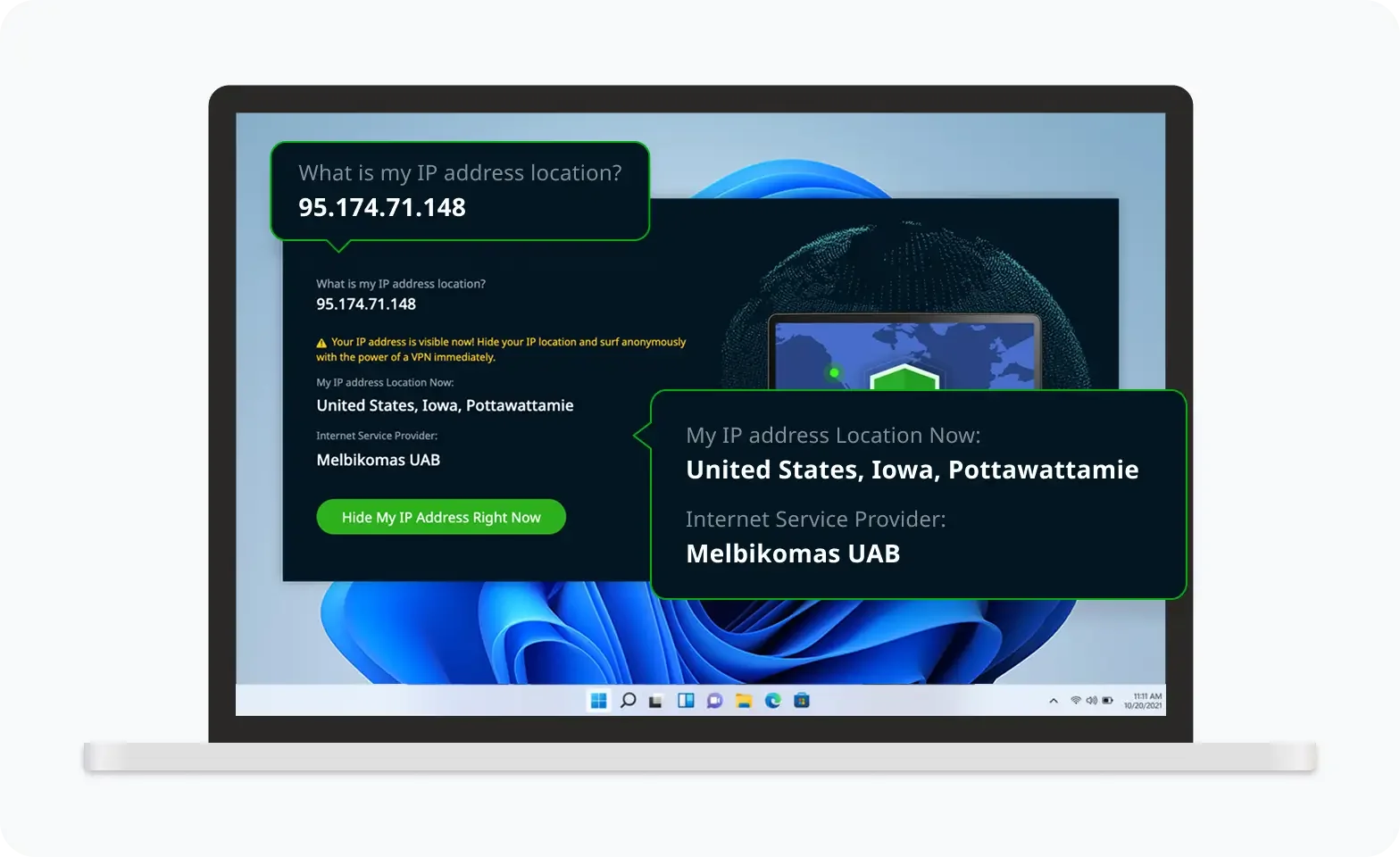
Verify Your IP Now
Use UFO VPN's " What is My IP " feature to see your new IP and location. This confirms your connection is secure, anonymous, and ready for safe browsing online anywhere at any time.

FAQs
How can I tell if a file is a zip bomb?
You can usually tell by the file's unusually small size compared to the uncompressed data. A zip bomb will have a high compression ratio, meaning it can contain massive amounts of data in a small package.
Can I open a zip bomb safely?
You should never open a zip bomb. Opening it can overwhelm your device’s memory and cause serious damage. If you suspect a file may be a zip bomb, avoid extracting it.
How does UFO VPN help protect against zip bombs?
UFO VPN encrypts your internet connection, ensuring that your browsing activities are private and secure. While it won’t directly prevent zip bombs, it helps keep your data safe from malicious actors trying to send harmful files.
Are zip bombs detectable by antivirus software?
Yes, most modern antivirus software can detect zip bombs before they are unpacked, protecting your system from the majority of these threats.