What Is an IP Stresser? What Is an IP Booter?

At their core, an IP stresser is a service designed to generate large volumes of traffic toward a target IP or domain to test its capacity and resilience under load . Originally legitimate tools for network administrators, many stressers have been repurposed as IP booters, marketed explicitly for launching DDoS attacks against third‑party targets.
-
IP Stresser (Legitimate Use): Licensed services used by companies and security professionals to simulate traffic surges—such as Black Friday sales or gaming tournaments—to validate load‑balancers, capacity planning, and DDoS mitigation systems.
-
IP Booter (Malicious Use): Underground or semi‑public services offering “DDoS‑for‑hire,” allowing anyone—typically for a small fee—to flood a victim’s server and disrupt online operations.
Common “Free IP Stresser” Models:
-
Time‑Limited Trials: Many booters let you launch a one‑minute attack for free to showcase power.
-
Captcha or Quiz Gate: Complete quick tasks (e.g., solve a captcha) to unlock a short free test.
-
Referral Bonuses: Earn additional free credits by referring new users.
While stress‑testing your own systems is permissible, using these tools against others without consent is illegal in most countries.
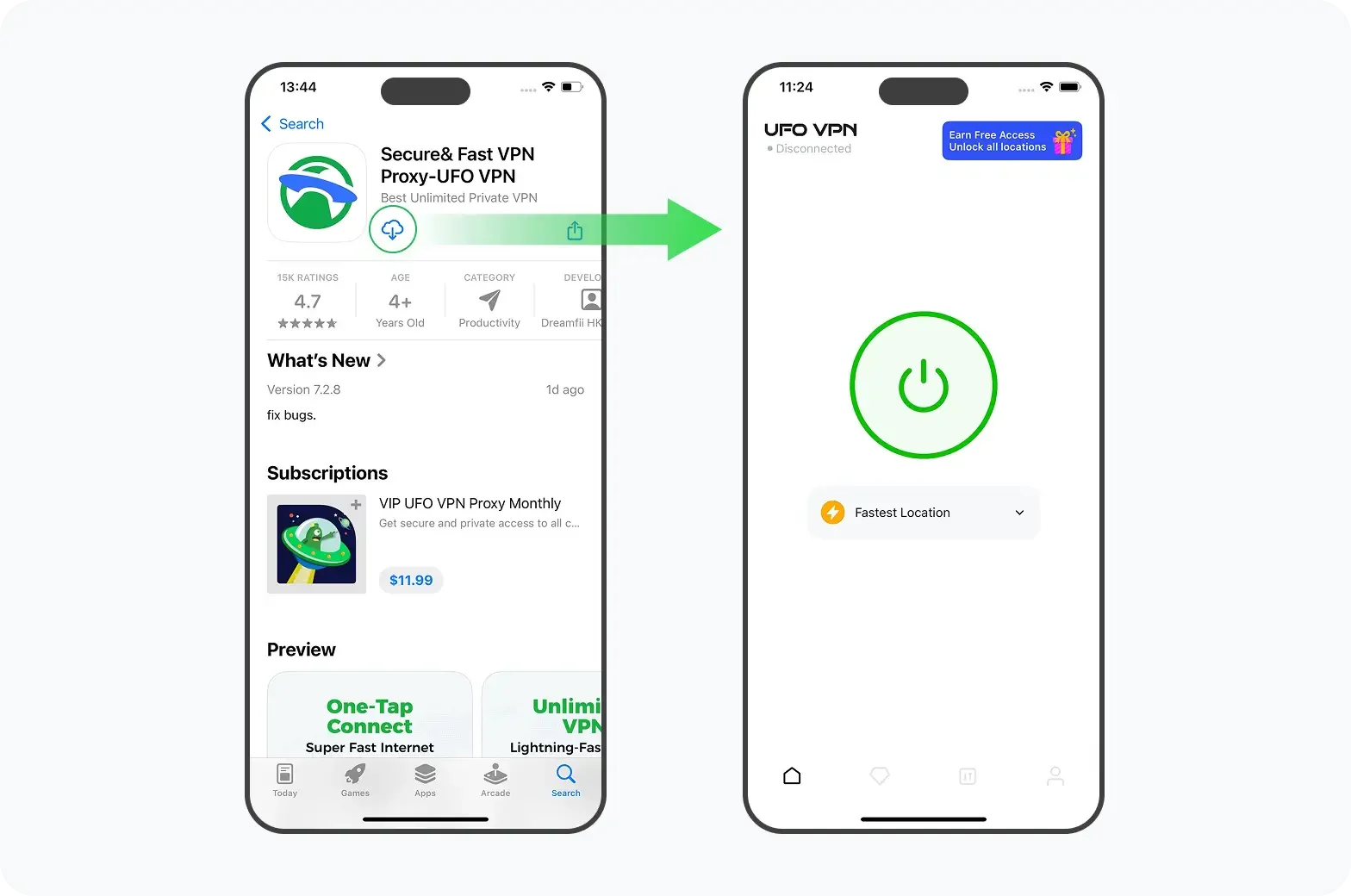
👾LIMITED TIME DISCOUNT: If you're in the heavily internet-regulated region of India, we've got you covered with a free and secure India VPN that's compatible with both your Apple and Android devices. Just download free VPN for Android - UFO VPN (with VPN APK) and free iPhone VPN - UFO VPN for iOS.
Are IP Stressers Legal?
The legality of free IP stressers hinges on authorization and intent:
-
Authorized Testing (Legal):
-
You own or have explicit permission from the owner to stress‑test a network. This usage falls under “white‑hat” security auditing and is widely accepted.
-
-
Unauthorized Attacks (Illegal):
-
Flooding someone else’s server without permission violates computer misuse laws—such as the U.S. Computer Fraud and Abuse Act (CFAA) or the UK’s Computer Misuse Act . Perpetrators risk criminal charges, fines, and imprisonment.
-
Real‑World Enforcement Examples:
-
Operation Power Off (2018): The U.S. Department of Justice dismantled several booter services, seizing domains and arresting operators who facilitated millions of DDoS attacks .
-
European Takedowns: Europol’s Operation “Megaboot” shut down multiple booter sites, highlighting cross‑border cooperation against illicit DDoS services .
Key Takeaway: If you’re using a “free IP stresser,” ensure it’s against systems you control. Launching against third‑party targets is a prosecutable offense.

[[[ 1 + base-article-card ]]]
How Does an IP Stresser Work?
An IP stresser/IP booter weaponizes large‑scale traffic generation through these components:
-
User Front End:
-
A web dashboard where attackers enter the target IP/domain, choose the attack method, and specify duration/intensity.
-
-
Attack Infrastructure:
-
Botnets: Networks of compromised devices (IoT, routers, PCs) that execute small tasks until commanded to flood a target with TCP, UDP, or HTTP requests.
-
Cloud Servers: Booter operators rent or own high‑bandwidth servers to generate traffic—often more reliable and easier to scale.
-
-
Attack Types:
-
Volumetric Floods: UDP amplification (DNS, NTP), reflection attacks that multiply traffic volume.
-
Protocol Attacks: TCP SYN floods, ACK/FIN attacks targeting server resources.
-
Application‑Layer Floods: HTTP GET/POST floods aimed at exhausting web server processes.
-
-
Traffic Spoofing & Obfuscation:
-
Spoofed source IP addresses to mask the true origin and evade basic IP‑based blocking.
-
-
Command & Control (C&C):
-
Operators control botnets via encrypted channels (IRC, custom protocols), coordinating distributed traffic surges.
-
Attack Lifecycle:
-
Attacker logs into the booter portal.
-
Chooses “UDP Amplification” for a free IP stresser test.
-
Enters victim’s gaming server IP—often found via in‑game console.
-
Clicks “Launch.” Within seconds, the victim experiences latency spikes or complete outage.
Should You Use a VPN to Protect Yourself from a DDoS Attack?
While a VPN cannot fully neutralize a large DDoS, it offers key defenses against IP stresser‑style attacks:
-
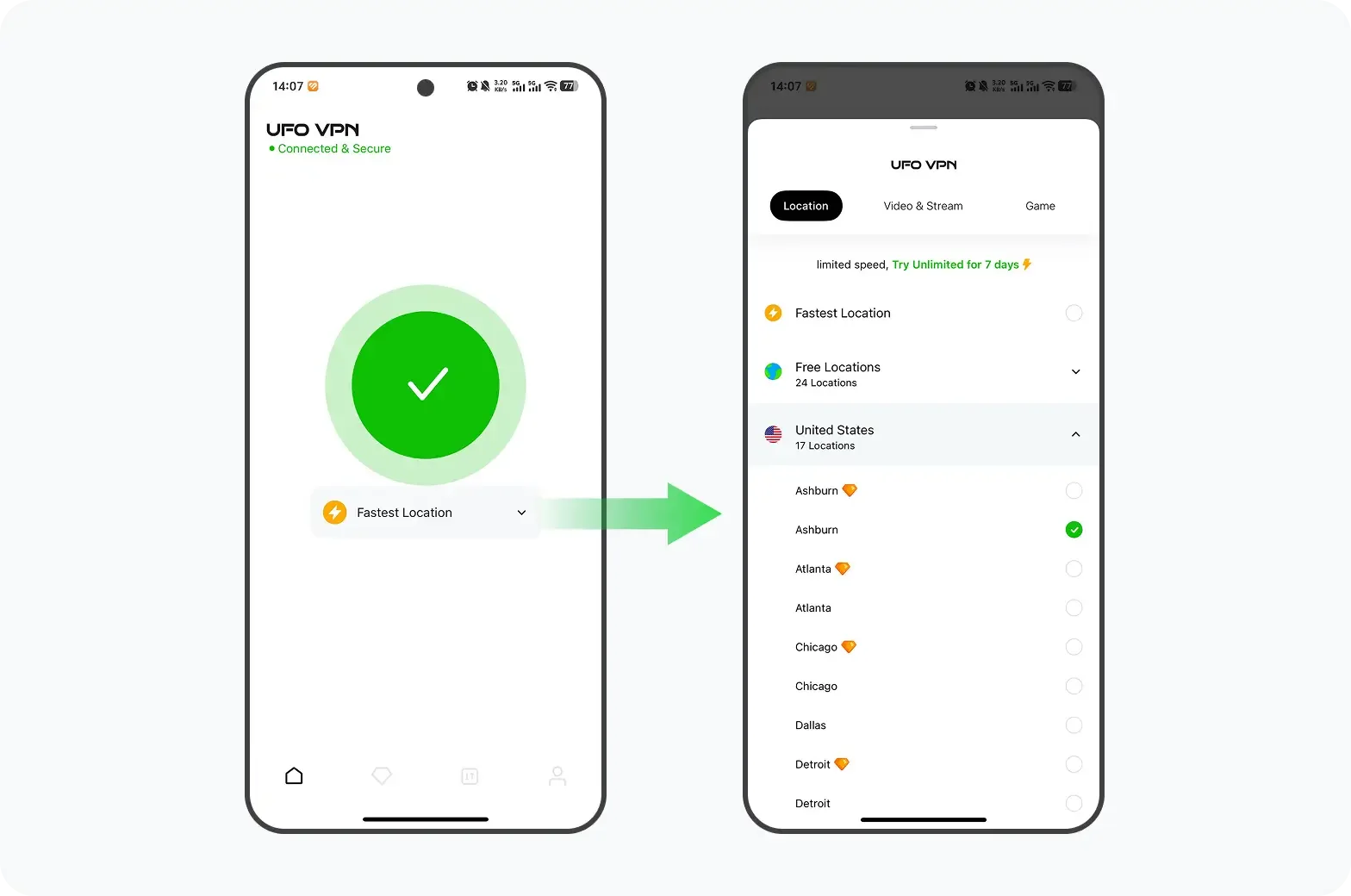
IP Concealment & Rotation:
-
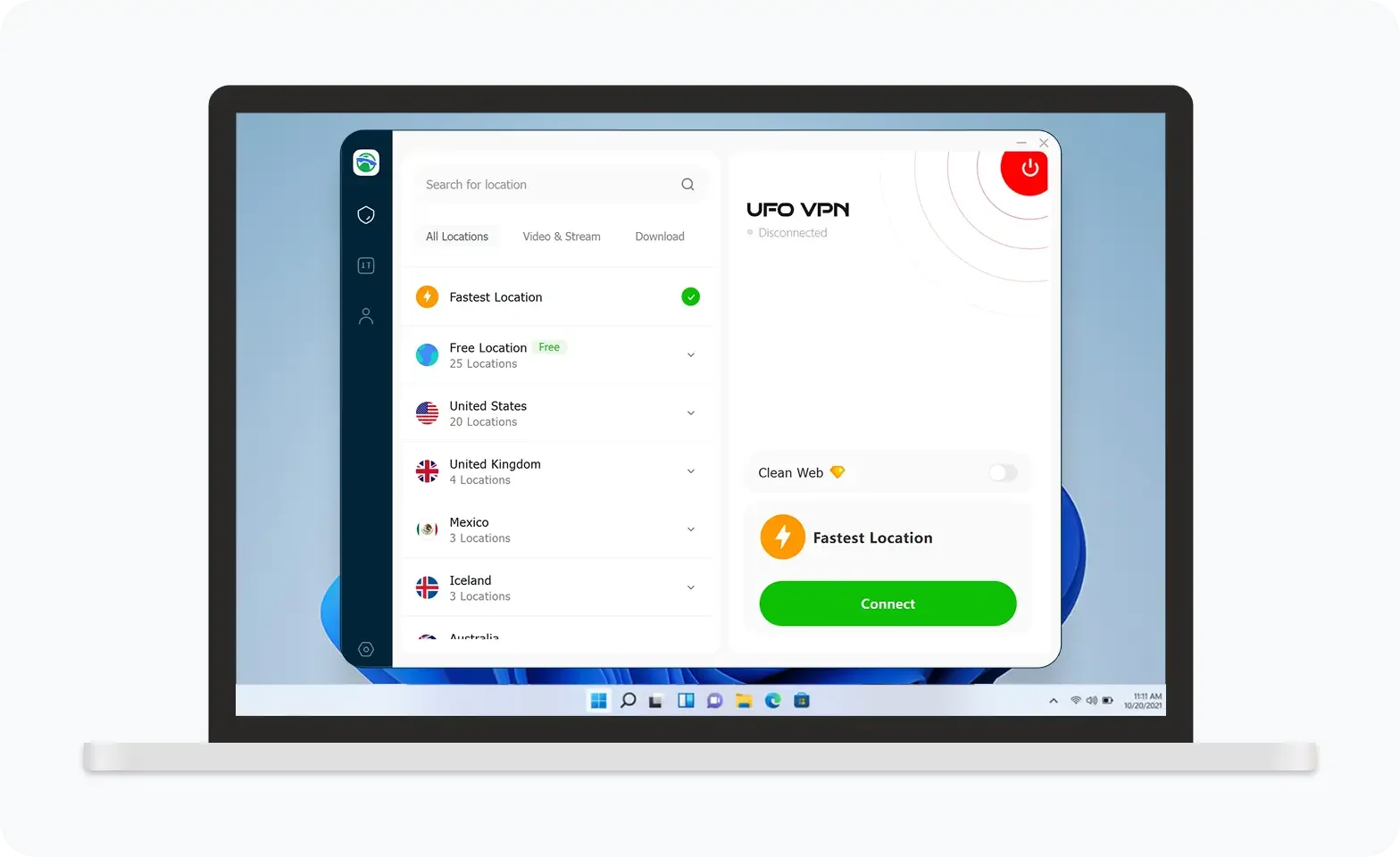
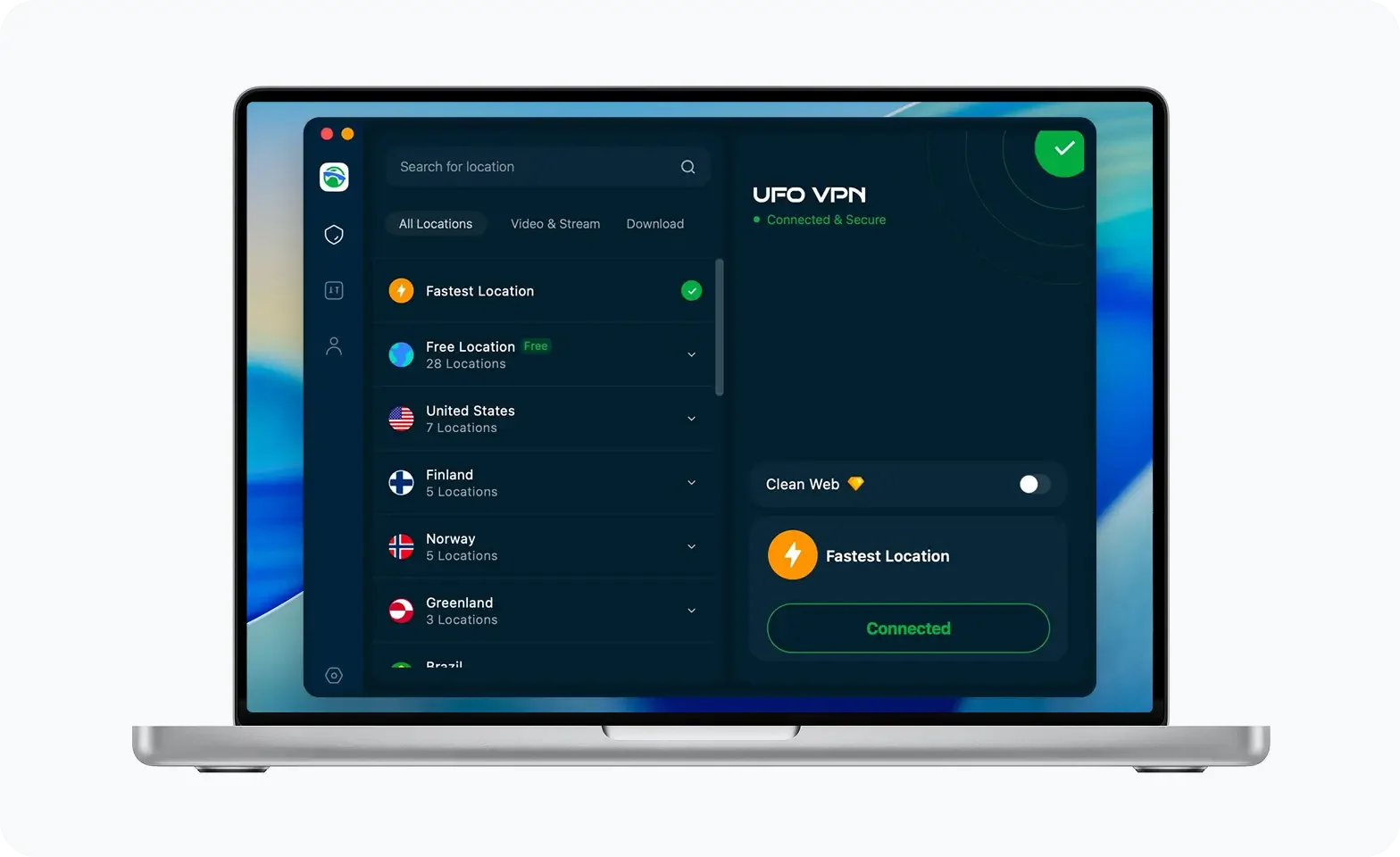
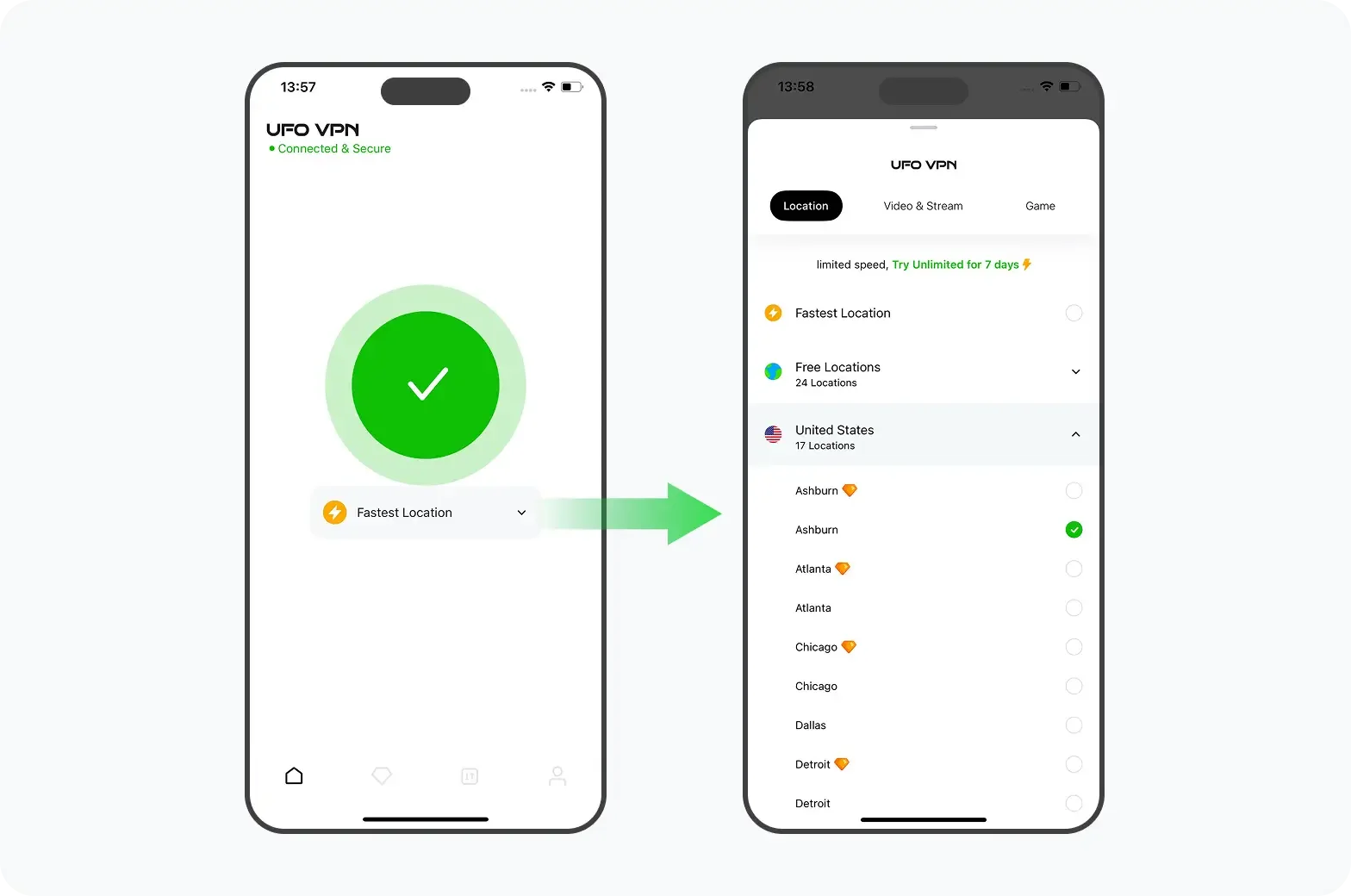
A reputable VPN like UFO VPN masks your real IP behind its server pool. Changing servers rotates your public IP, making it harder for attackers to target you.
-
-
Traffic Scrubbing & Redistribution:
-
VPN servers can distribute incoming traffic across multiple data centers, diluting attack intensity before it reaches your endpoint.
-
-
Encrypted Tunnels:
-
VPN encryption blocks attackers from intercepting DNS or application data used for sophisticated application‑layer floods.
-
-
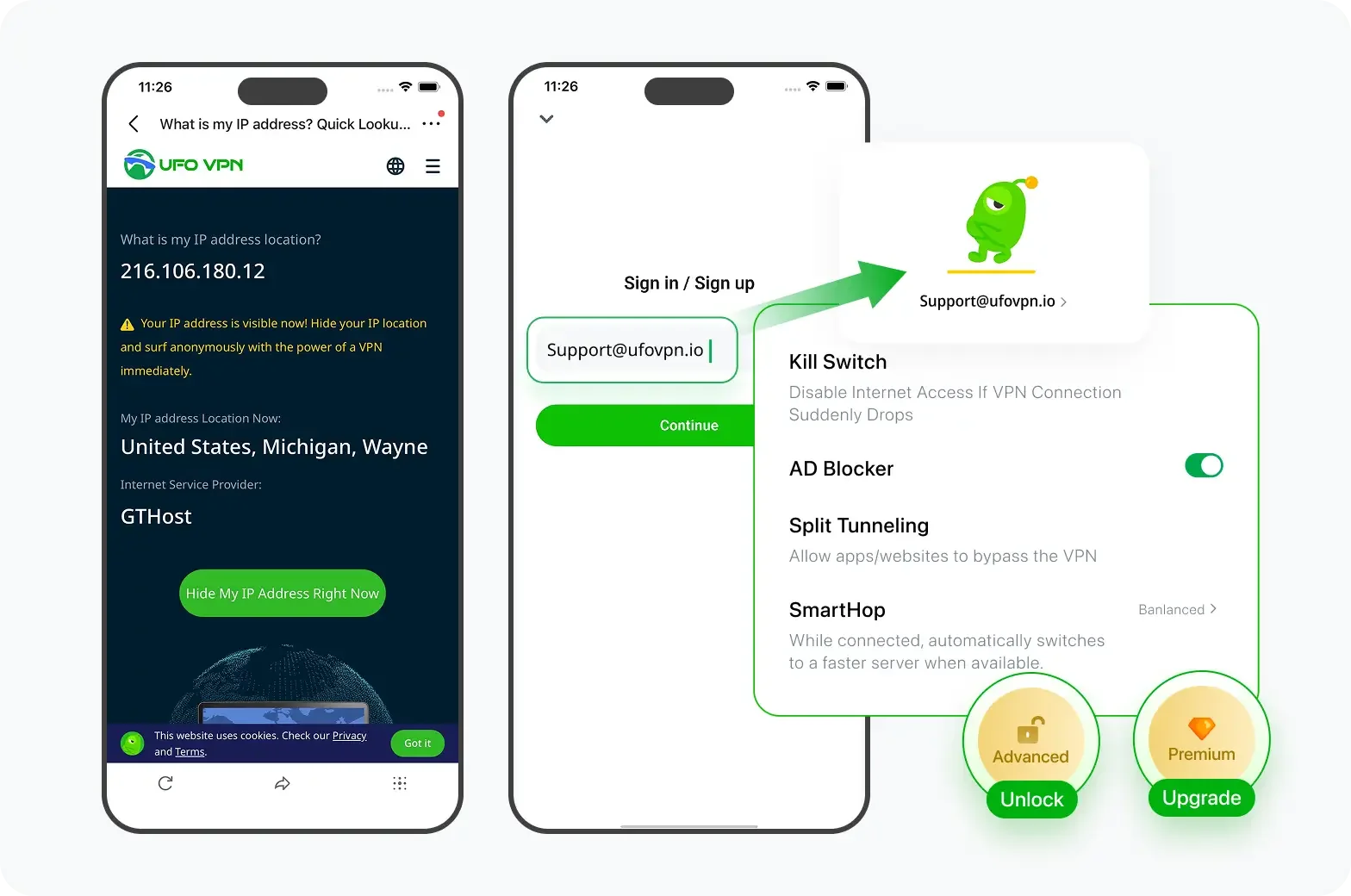
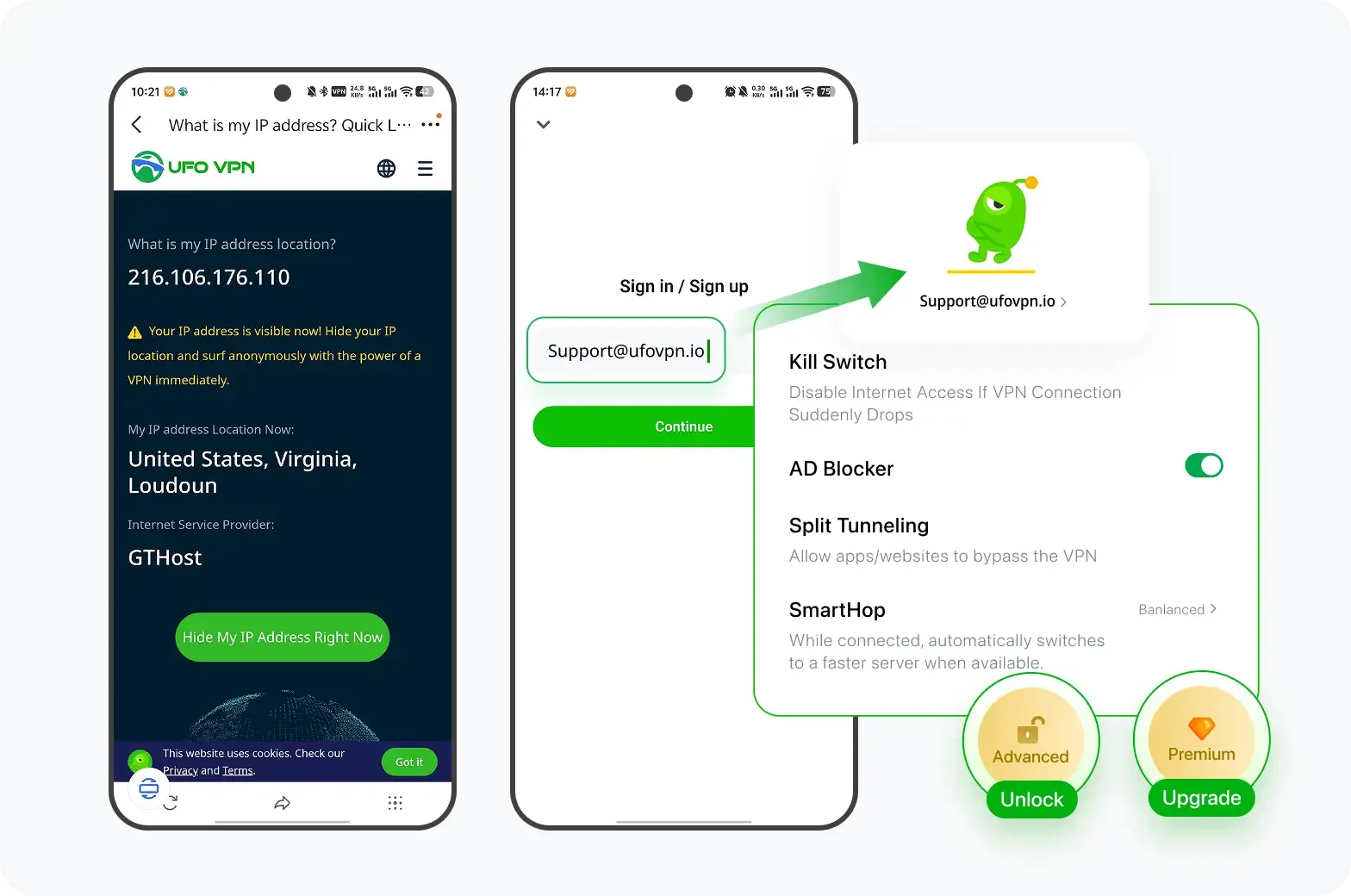
Kill Switch:
-
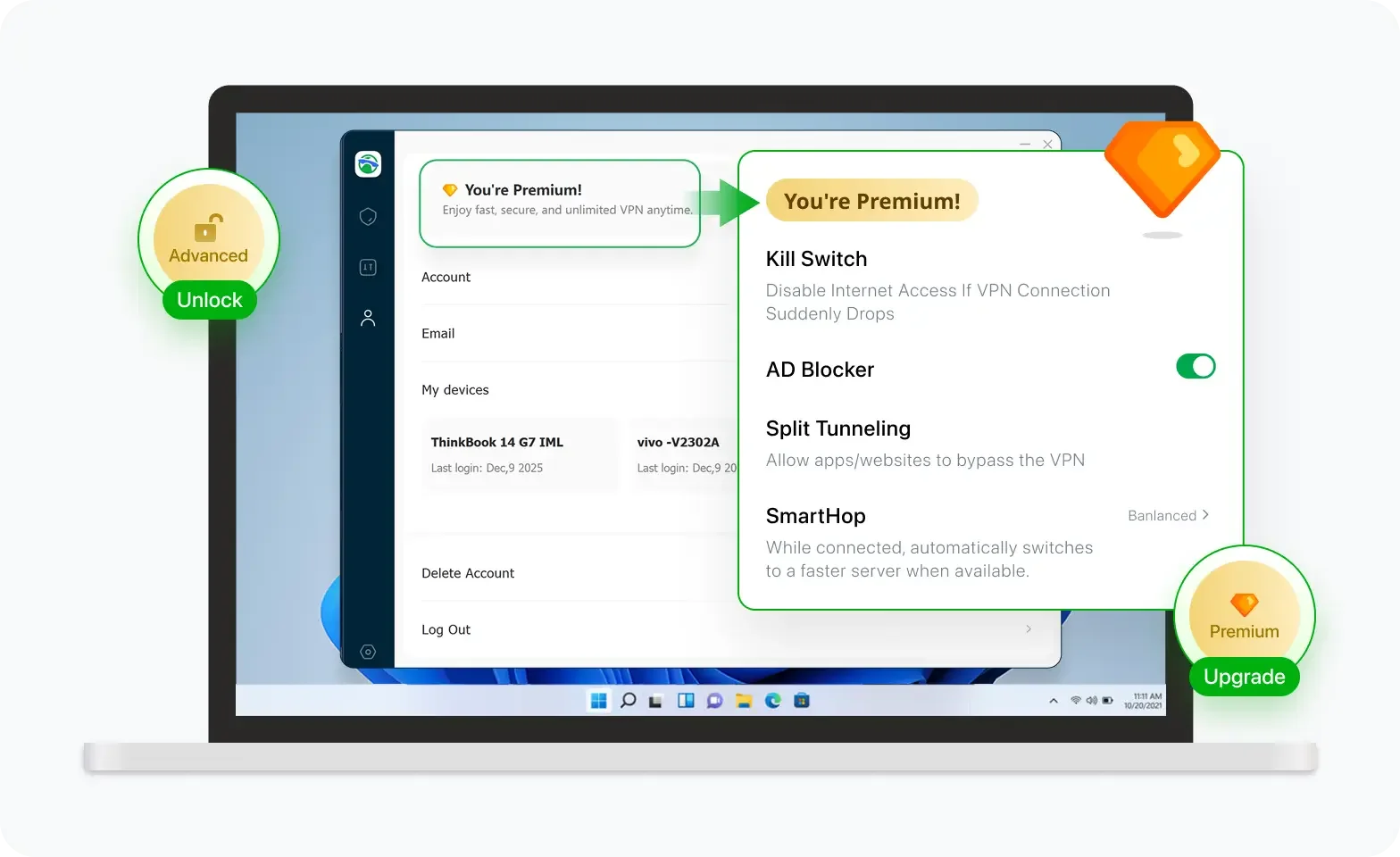
UFO VPN’s kill switch halts all traffic if the VPN disconnects—preventing your true IP from leaking mid‑attack.
-
-
Multi‑Hop Routing:
-
Advanced features route traffic through multiple VPN nodes, adding latency for attackers to overcome.
-
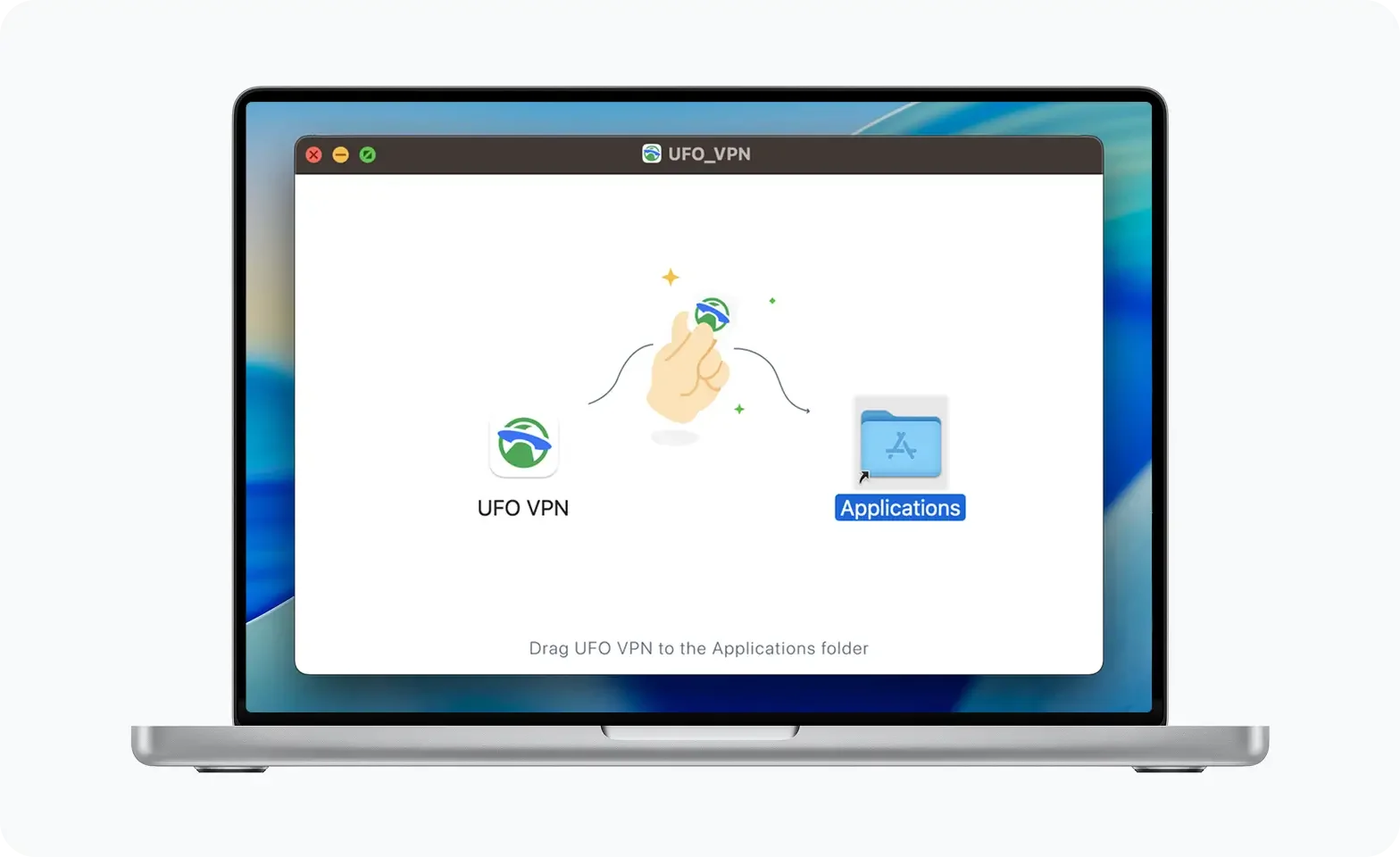
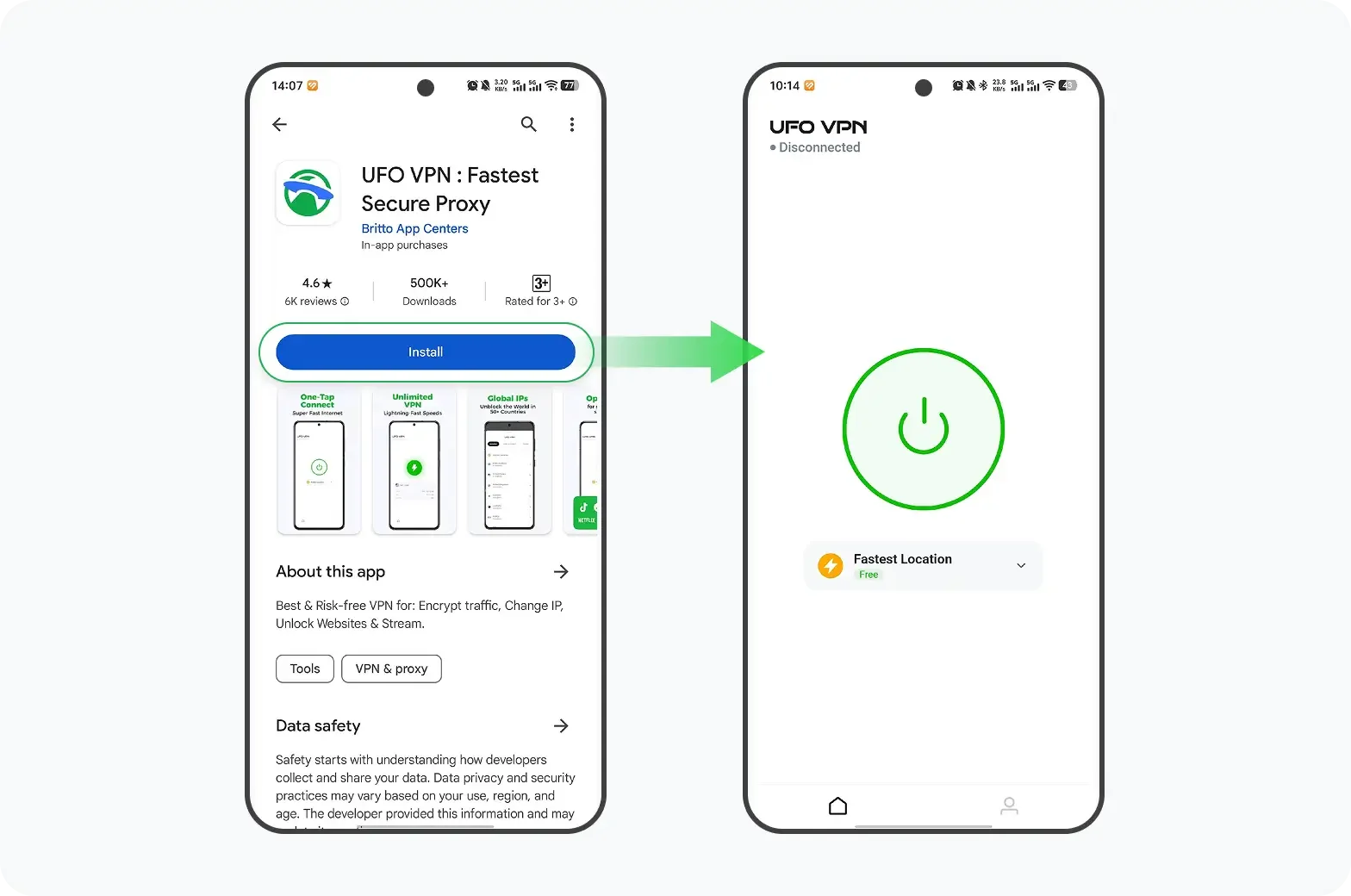
Implementation Steps:
UFO VPN is an all-in-one VPN that offers unlimited access to 4K streaming like Netlfix, Disney Plus, no-ping gaming as PUBG, Roblox, CODM and social networking for YouTube, X, Facebook and more.
Unlock Pro Features
If you have upgraded to premium plan , feel free to enjoy premium servers for 4K streaming and advanced features like Kill Switch, Split Tunneling, and gaming acceleration. Your Mac is now fully optimized and protected. Inaddition to basic functions, we recommend you turn on

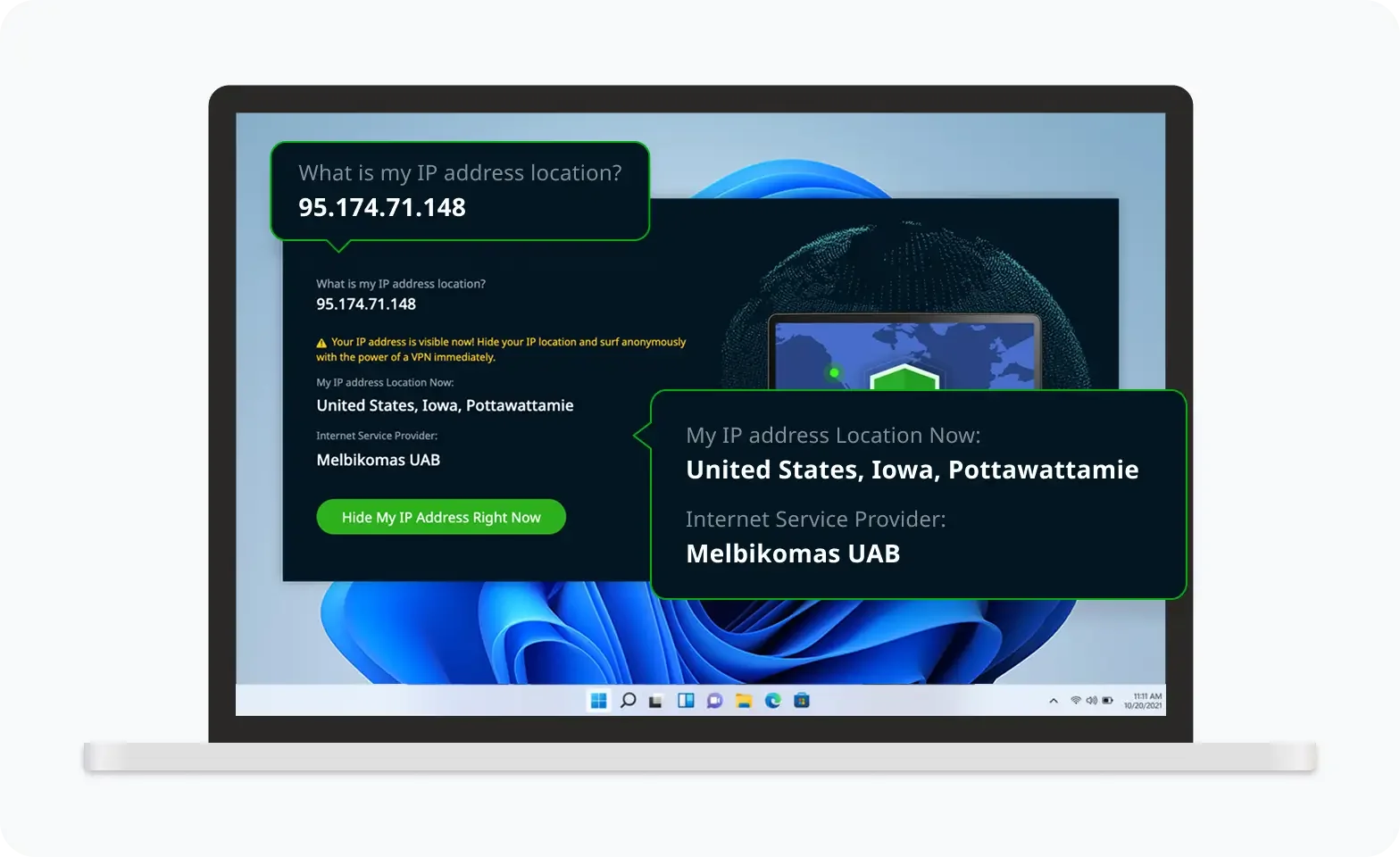
Verify Your IP Now
Use UFO VPN's " What is My IP " feature to see your new IP and location. This confirms your connection is secure, anonymous, and ready for safe browsing online anywhere at any time.

While no solution guarantees absolute protection, combining a VPN with DDoS‑ready hosting or a dedicated hardware appliance significantly raises the barrier for attackers using free IP stressers.
Defense & Mitigation Strategies Beyond VPN

A holistic DDoS defense involves layered tactics:
-
Web Application Firewalls (WAF): Block known malicious request patterns at the HTTP layer.
-
Rate Limiting & CAPTCHA: Throttle suspicious traffic or challenge bots with CAPTCHAs for application‑layer attacks.
-
Traffic Filtering & Null Routing: Blackhole attack traffic at the ISP level using BGP announcements.
-
Anycast & CDN Services: Distribute incoming traffic globally to high‑capacity points of presence (e.g., Cloudflare, Akamai).
-
Botnet Monitoring: Leverage threat intelligence feeds to pre‑emptively block known botnet IP ranges.
-
Legal & Incident Response: Retain logs, contact your ISP for upstream filtering, and report abuse to law enforcement.
FAQs
Q1: What’s the difference between a free IP stresser and a paid booter?
Free offerings are time‑limited “samples” designed to upsell paid plans. Paid booters provide higher bandwidth, more attack methods, and longer durations.
Q2: Can I buy DDoS protection as a service?
Yes—services like Cloudflare Spectrum or AWS Shield Advanced offer turnkey DDoS mitigation at scale, though at enterprise pricing.
Q3: Are mobile VPNs effective against DDoS?
They help mask mobile device IPs but aren’t sufficient if attackers target your primary public IP (e.g., home router). Router‑level VPNs or cloud‑based scrubbing are stronger.
Q4: How do I check if I’m under a DDoS attack?
Look for unusual traffic spikes in your router/firewall dashboard, unresponsive services, or ICMP/ping floods. Monitoring tools like Zabbix or Netdata can alert you in real time.
Q5: Is it possible to launch a DDoS against a VPN server?
Yes, but reputable VPN providers use large server clusters and DDoS‑protection measures, making it hard to overwhelm them.
Q6: Can I legally report someone using a booter against me?
Absolutely—contact your ISP to trace incoming traffic, file an abuse report, and involve law enforcement with your network logs.